-
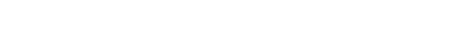
In response to the demand for identity authentication in quantum secure direct communication, this paper proposes a quantum secure direct communication scheme based on a mixture of single photon and Bell state, by combining the bidirectional identity authentication. Before communication begins, both parties share a series of secret information to prepare a series of single photon and Bell state particles. Encoding four single photons and four Bell states yields eight types of encoded information, followed by identity authentication. The first step in identity authentication is to use a single photon to verify the legitimacy of the receiver. If the error exceeds the given threshold, it indicates the presence of eavesdropping. Otherwise, the channel is safe. Then, Bell state particles are used to verify the legitimacy of the sender, and the threshold is also used to determine whether there is eavesdropping. The present method is the same as previous one. If the error rate is higher than the given threshold, it indicates the existence of third-party eavesdropping. Otherwise, it indicates that the channel is secure. As for the specific verification method, it will be explained in detail in the article. Afterwards, Bell state particles are mixed with a single photon as a transmission carrier, and eavesdropping detection particles are added whenever the quantum state is sent. However, once the eavesdropper intercepts the transmitted particles, owing to incomplete information obtained, the eavesdropper is unable to recover the original information, and the eavesdropping behavior will be immediately detected, thus terminating communication. In this scheme, single photon and Bell states are fully utilized, and hybrid communication can effectively improve transmission efficiency, encoding capability, and quantum bit utilization. Security analysis shows that this scheme can resist common external and internal attacks such as interception/measurement replay attacks, auxiliary particle attacks, and identity impersonation attacks. The analysis of efficiency and encoding capacity shows that the transmission efficiency of this scheme is 1, the encoding capacity is 3 bits per state, and the quantum bit utilization rate is 1. Compared with other schemes, this scheme has significant advantages because it uses different particles for bidirectional authentication, making it more difficult for attackers to crack, and thus it has higher security than traditional schemes.
-
Keywords:
- quantum secure direct communication /
- mixed state /
- identity authentication /
- transmission efficiency
[1] Bennett C H, Brassard G 1984 Proceedings of the IEEE International Conference on Computers, Systems, and Signal Processing (New York: IEEE Press) p175
[2] Ekert A K 1991 Phys. Rev. Lett. 67 661
 Google Scholar
Google Scholar
[3] Kwek L C, Cao L, Luo W, Wang Y X, Sun S H, Wang X B, Liu A Q 2021 AAPPS Bull. 31 15
 Google Scholar
Google Scholar
[4] Guo H, Li Z Y, Yu S, Zhang Y C 2021 Fundament. Res. 1 96
 Google Scholar
Google Scholar
[5] Gerhardt I, Liu Q, Lamas-Linares A, Skaar J, Kurtsiefer C, Makarov V 2011 Nat. Commun. 2 349
 Google Scholar
Google Scholar
[6] Beige A, Englert B G, Kurtsiefer C 2002 J. Phys. A Math. Gen. 35 L407
 Google Scholar
Google Scholar
[7] Quan D X, Zhu C H, Liu S Q, Pei C X 2015 Chin. Phys. B 24 256
 Google Scholar
Google Scholar
[8] Li Y B, Song T T, Huang W 2015 Internat. J. Theoretical Phys. 54 589
 Google Scholar
Google Scholar
[9] Long G L, Liu X S 2002 Phys. Rev. A 65 032302
 Google Scholar
Google Scholar
[10] Deng F G, Long G L, Liu X S 2003 Phys. Rev. A 68 042317
 Google Scholar
Google Scholar
[11] Deng F G, Long G L 2004 Phys. Rev. A 69 052319
 Google Scholar
Google Scholar
[12] Wang C, Deng F G, Li Y S 2005 Phys. Rev. A 71 044305
 Google Scholar
Google Scholar
[13] Wang J, Zhang Q, Tang C J 2006 Phys. Lett. A 358 256
 Google Scholar
Google Scholar
[14] Man Z X, Xia Y J 2007 Chin. Phys. Lett. 24 15
 Google Scholar
Google Scholar
[15] Lan M, Shao T N, Xie J L, Yang X F, Sun K, Cai T T, Wang J Z 2011 Sci. China Phys. Mech. Astron. 54 942
 Google Scholar
Google Scholar
[16] 李凯, 黄晓英, 滕吉红, 李振华 2012 电子与信息学报 34 1917
 Google Scholar
Google Scholar
Li K, Huang X Y, Teng J H, Li Z H 2012 J. Electron. Inf. Tech. 34 1917
 Google Scholar
Google Scholar
[17] 安辉耀, 刘敦伟, 耿瑞华, 曾和平, 赵林欣 2016 系统工程与电子技术 38 1917
An H Y, Liu D W, Geng R H, Zeng H P, Zhao L X 2016 Syst. Eng. Electron. Tech. 38 1917
[18] 龙桂鲁 2015 十一届全国光学前沿研讨会 长沙 2015-10-09 p21
Long G L 2015 The 11 th National Symposium on Optical Frontiers Changsha, China, October 9, 2015 p21 (in Chinese)
[19] Hu J Y, Yu B, Jing M Y, Xiao L T, Jia S T, Qin G Q, Long G L 2016 Light Sci. Appl. 5 e16144
 Google Scholar
Google Scholar
[20] Zhang W, Ding D S, Sheng Y B, Zhou L, Shi B S, Guo G C 2017 Phys. Rev. Lett. 118 220501
 Google Scholar
Google Scholar
[21] Zhu F, Zhang W, Sheng Y B, Huang Y D 2017 Sci. Bull. 62 1519
 Google Scholar
Google Scholar
[22] 曹正文, 赵光, 张爽浩, 冯晓毅, 彭进业 2016 65 230301
 Google Scholar
Google Scholar
Cao Z W, Zhao G, Zhang S H, Feng X Y, Peng J Y 2016 Acta Phys. Sin. 65 230301
 Google Scholar
Google Scholar
[23] 刘志昊, 陈汉武 2017 66 130304
 Google Scholar
Google Scholar
Liu Z H, Chen H W 2017 Acta Phys. Sin. 66 130304
 Google Scholar
Google Scholar
[24] 赵宁, 江英华, 周贤韬, 郭晨飞, 刘彪 2021 网络安全技术与应用 8 30
 Google Scholar
Google Scholar
Zhao N, Jiang Y H, Zhou X T, Guo C F, Liu B 2021 Network Security Technology 8 30
 Google Scholar
Google Scholar
[25] 周贤韬, 江英华, 郭晨飞, 赵宁, 刘彪 2021 量子电子学报 39 768
 Google Scholar
Google Scholar
Zhou X T, Jiang Y H, Guo C F, Zhao N, Liu B 2021 Chin. J. Quantum Electron. 39 768
 Google Scholar
Google Scholar
[26] 周贤韬, 江英华 2022 激光技术 46 79
 Google Scholar
Google Scholar
Zhou X T, Jiang Y H 2022 Laser Technol. 46 79
 Google Scholar
Google Scholar
[27] 赵宁, 江英华, 周贤韬 2022 71 150304
 Google Scholar
Google Scholar
Zhao N, Jiang Y H, Zhou X T 2022 Acta Phys. Sin. 71 150304
 Google Scholar
Google Scholar
[28] 龚黎华, 陈振泳, 徐良超, 周南润 2022 71 130304
 Google Scholar
Google Scholar
Gong L H, Chen Z Y, Xu L C, Zhou N R 2022 Acta Phys. Sin. 71 130304
 Google Scholar
Google Scholar
[29] Qi R Y, Sun Z, Lin Z S, Niu P H, Hao W T, Song L Y, Huang Q, Gao J C, Yin L G, Long G L 2019 Light Sci. Appl. 8 22
 Google Scholar
Google Scholar
[30] Zhang H R, Sun Z, Qi R Y, Yin L G, Long G L, Lu J H 2022 Light Sci. Appl. 11 83
 Google Scholar
Google Scholar
[31] Wang C 2021 Fundament. Res. 1 91
 Google Scholar
Google Scholar
-
表 1 编码规则
Table 1. Coding rules.
单光子 表示的经典信息 Bell态 表示的经典信息 $ | 0 \rangle $ 000 $ | {{\psi ^ + }} \rangle $ 010 $| 1 \rangle $ 111 $ | {{\psi ^ - }} \rangle $ 101 $ | + \rangle $ 001 $| {{\varphi ^ + }} \rangle $ 011 $ | - \rangle $ 110 $| {{\varphi ^ - }} \rangle $ 100 表 2 基于单光子身份认证过程
Table 2. Single photon based identity authentication process.
1 2 3 4 秘钥K 1 0 0 1 序列$ {S_n} $量子态 $ | + \rangle $ $ | 0 \rangle $ $ | 0 \rangle $ $ | + \rangle $ 合法Alice根据K
选测量基X Z Z X 合法Alice测量结果 $ | + \rangle $ $ | 0 \rangle $ $ | 0 \rangle $ $ | + \rangle $ 冒充Alice测量结果
(随机选择测量基)50%$ | + \rangle $
25%$ | 0 \rangle $
25%$ | 1 \rangle $50%$ | 0 \rangle $
25%$ | + \rangle $
25%$ | - \rangle $50%$ | 0 \rangle $
25%$ | + \rangle $
25%$ | - \rangle $50%$ | + \rangle $
25%$ | 0 \rangle $
25%$ | 1 \rangle $表 3 基于Bell态身份认证过程
Table 3. Identity authentication process based on Bell state.
${\varphi }^{+}或{\varphi }^{-}$在$ {S}_{1} $中位置 1 4 5 9 11 12 15 17 18 $ \cdots $ 量子态 $ |0 \rangle $ $ | + \rangle $ $ |0 \rangle $ $ | + \rangle $ $ |- \rangle $ $ |1 \rangle $ $ |0 \rangle $ $ |- \rangle $ $ | + \rangle $ $ \cdots $ 共享秘钥K 1 0 0 1 Alice公布位置L 4 5 15 18 根据K选择测量基 X Z Z X 合法Bob测量结果 $ | + \rangle $ $ |0 \rangle $ $ |0 \rangle $ $ | + \rangle $ 冒充Bob 测量结果 $50{\text{%}} | + \rangle $
$25{\text{%}} |0 \rangle $
$25{\text{%}} |1 \rangle $$ 50{\text{%}}|0 \rangle $
$25{\text{%}} | + \rangle $
$25{\text{%}} |- \rangle $$ 50{\text{%}}|0 \rangle $
$ 25{\text{%}} | + \rangle $
$25{\text{%}} |- \rangle $$50{\text{%}} | + \rangle $
$25{\text{%}} |0 \rangle $
$25{\text{%}} |1 \rangle $表 4 信息传输过程
Table 4. Information transmission process.
1 2 3 4 5 6 7 8 秘密信息M 010 111 011 110 011 110 000 100 混合态序列${S}_{1-S}$量子态 $ \left| {{\psi ^ + }} \right\rangle $ $ \left| 1 \right\rangle $ $\left| {{\varphi ^ + }} \right\rangle $ $ \left| - \right\rangle $ $\left| {{\varphi ^ + }} \right\rangle $ $ \left| - \right\rangle $ $ \left| 0 \right\rangle $ $\left| {{\varphi ^ - }} \right\rangle $ Alice公布的测量基 Bell基 Z基 Bell基 X基 Bell基 X基 Z基 Bell基 Bob测量结果 $ \left| {{\psi ^ + }} \right\rangle $ $ \left| 1 \right\rangle $ $\left| {{\varphi ^ + }} \right\rangle $ $ \left| - \right\rangle $ $\left| {{\varphi ^ + }} \right\rangle $ $ \left| - \right\rangle $ $ \left| 0 \right\rangle $ $\left| {{\varphi ^ - }} \right\rangle $ 解码得信息M 010 111 011 110 011 110 000 100 表 5 各方案参数对比
Table 5. Comparison of parameters of various schemes.
-
[1] Bennett C H, Brassard G 1984 Proceedings of the IEEE International Conference on Computers, Systems, and Signal Processing (New York: IEEE Press) p175
[2] Ekert A K 1991 Phys. Rev. Lett. 67 661
 Google Scholar
Google Scholar
[3] Kwek L C, Cao L, Luo W, Wang Y X, Sun S H, Wang X B, Liu A Q 2021 AAPPS Bull. 31 15
 Google Scholar
Google Scholar
[4] Guo H, Li Z Y, Yu S, Zhang Y C 2021 Fundament. Res. 1 96
 Google Scholar
Google Scholar
[5] Gerhardt I, Liu Q, Lamas-Linares A, Skaar J, Kurtsiefer C, Makarov V 2011 Nat. Commun. 2 349
 Google Scholar
Google Scholar
[6] Beige A, Englert B G, Kurtsiefer C 2002 J. Phys. A Math. Gen. 35 L407
 Google Scholar
Google Scholar
[7] Quan D X, Zhu C H, Liu S Q, Pei C X 2015 Chin. Phys. B 24 256
 Google Scholar
Google Scholar
[8] Li Y B, Song T T, Huang W 2015 Internat. J. Theoretical Phys. 54 589
 Google Scholar
Google Scholar
[9] Long G L, Liu X S 2002 Phys. Rev. A 65 032302
 Google Scholar
Google Scholar
[10] Deng F G, Long G L, Liu X S 2003 Phys. Rev. A 68 042317
 Google Scholar
Google Scholar
[11] Deng F G, Long G L 2004 Phys. Rev. A 69 052319
 Google Scholar
Google Scholar
[12] Wang C, Deng F G, Li Y S 2005 Phys. Rev. A 71 044305
 Google Scholar
Google Scholar
[13] Wang J, Zhang Q, Tang C J 2006 Phys. Lett. A 358 256
 Google Scholar
Google Scholar
[14] Man Z X, Xia Y J 2007 Chin. Phys. Lett. 24 15
 Google Scholar
Google Scholar
[15] Lan M, Shao T N, Xie J L, Yang X F, Sun K, Cai T T, Wang J Z 2011 Sci. China Phys. Mech. Astron. 54 942
 Google Scholar
Google Scholar
[16] 李凯, 黄晓英, 滕吉红, 李振华 2012 电子与信息学报 34 1917
 Google Scholar
Google Scholar
Li K, Huang X Y, Teng J H, Li Z H 2012 J. Electron. Inf. Tech. 34 1917
 Google Scholar
Google Scholar
[17] 安辉耀, 刘敦伟, 耿瑞华, 曾和平, 赵林欣 2016 系统工程与电子技术 38 1917
An H Y, Liu D W, Geng R H, Zeng H P, Zhao L X 2016 Syst. Eng. Electron. Tech. 38 1917
[18] 龙桂鲁 2015 十一届全国光学前沿研讨会 长沙 2015-10-09 p21
Long G L 2015 The 11 th National Symposium on Optical Frontiers Changsha, China, October 9, 2015 p21 (in Chinese)
[19] Hu J Y, Yu B, Jing M Y, Xiao L T, Jia S T, Qin G Q, Long G L 2016 Light Sci. Appl. 5 e16144
 Google Scholar
Google Scholar
[20] Zhang W, Ding D S, Sheng Y B, Zhou L, Shi B S, Guo G C 2017 Phys. Rev. Lett. 118 220501
 Google Scholar
Google Scholar
[21] Zhu F, Zhang W, Sheng Y B, Huang Y D 2017 Sci. Bull. 62 1519
 Google Scholar
Google Scholar
[22] 曹正文, 赵光, 张爽浩, 冯晓毅, 彭进业 2016 65 230301
 Google Scholar
Google Scholar
Cao Z W, Zhao G, Zhang S H, Feng X Y, Peng J Y 2016 Acta Phys. Sin. 65 230301
 Google Scholar
Google Scholar
[23] 刘志昊, 陈汉武 2017 66 130304
 Google Scholar
Google Scholar
Liu Z H, Chen H W 2017 Acta Phys. Sin. 66 130304
 Google Scholar
Google Scholar
[24] 赵宁, 江英华, 周贤韬, 郭晨飞, 刘彪 2021 网络安全技术与应用 8 30
 Google Scholar
Google Scholar
Zhao N, Jiang Y H, Zhou X T, Guo C F, Liu B 2021 Network Security Technology 8 30
 Google Scholar
Google Scholar
[25] 周贤韬, 江英华, 郭晨飞, 赵宁, 刘彪 2021 量子电子学报 39 768
 Google Scholar
Google Scholar
Zhou X T, Jiang Y H, Guo C F, Zhao N, Liu B 2021 Chin. J. Quantum Electron. 39 768
 Google Scholar
Google Scholar
[26] 周贤韬, 江英华 2022 激光技术 46 79
 Google Scholar
Google Scholar
Zhou X T, Jiang Y H 2022 Laser Technol. 46 79
 Google Scholar
Google Scholar
[27] 赵宁, 江英华, 周贤韬 2022 71 150304
 Google Scholar
Google Scholar
Zhao N, Jiang Y H, Zhou X T 2022 Acta Phys. Sin. 71 150304
 Google Scholar
Google Scholar
[28] 龚黎华, 陈振泳, 徐良超, 周南润 2022 71 130304
 Google Scholar
Google Scholar
Gong L H, Chen Z Y, Xu L C, Zhou N R 2022 Acta Phys. Sin. 71 130304
 Google Scholar
Google Scholar
[29] Qi R Y, Sun Z, Lin Z S, Niu P H, Hao W T, Song L Y, Huang Q, Gao J C, Yin L G, Long G L 2019 Light Sci. Appl. 8 22
 Google Scholar
Google Scholar
[30] Zhang H R, Sun Z, Qi R Y, Yin L G, Long G L, Lu J H 2022 Light Sci. Appl. 11 83
 Google Scholar
Google Scholar
[31] Wang C 2021 Fundament. Res. 1 91
 Google Scholar
Google Scholar
Catalog
Metrics
- Abstract views: 4525
- PDF Downloads: 109
- Cited By: 0













 DownLoad:
DownLoad:
