-
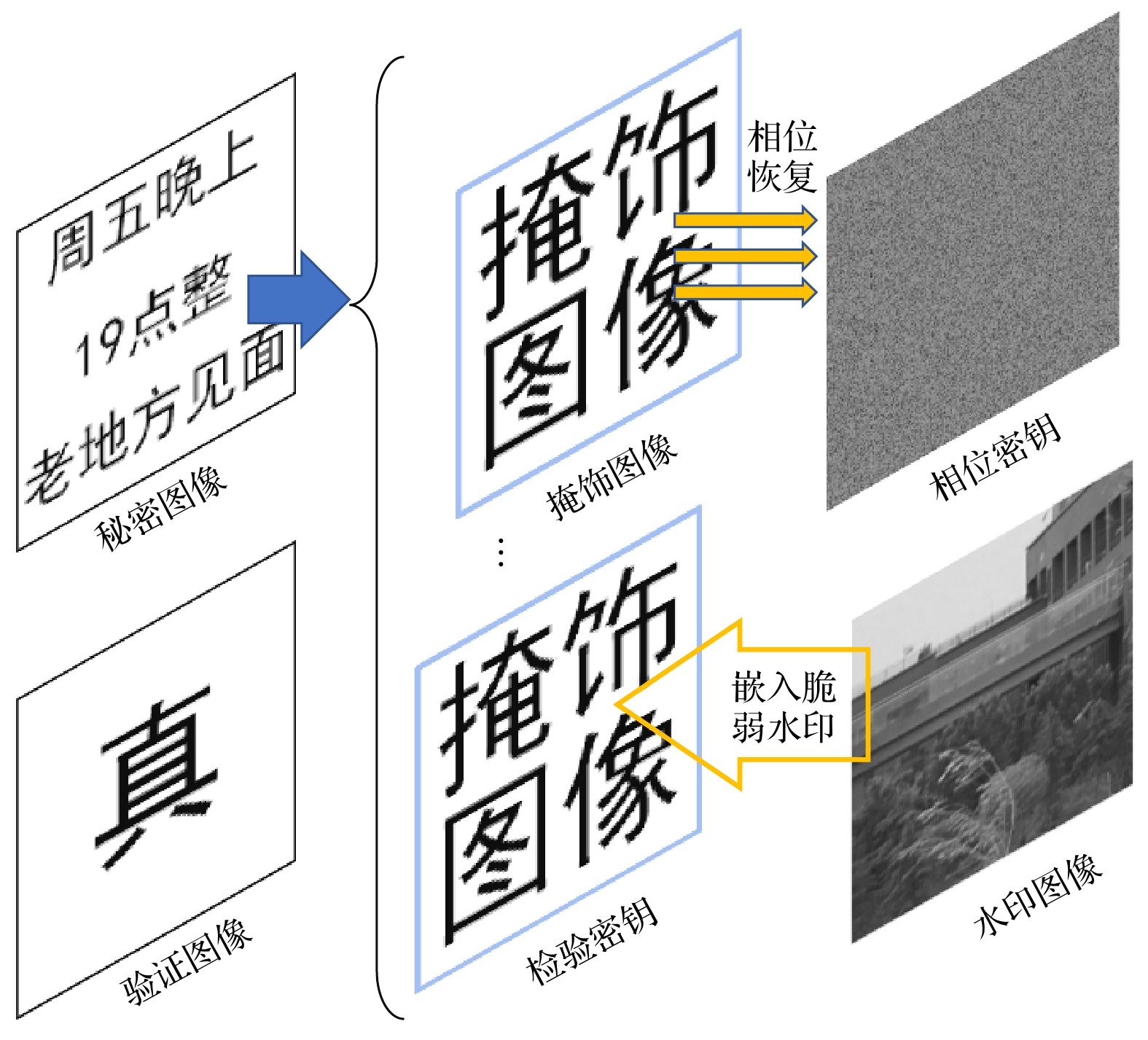
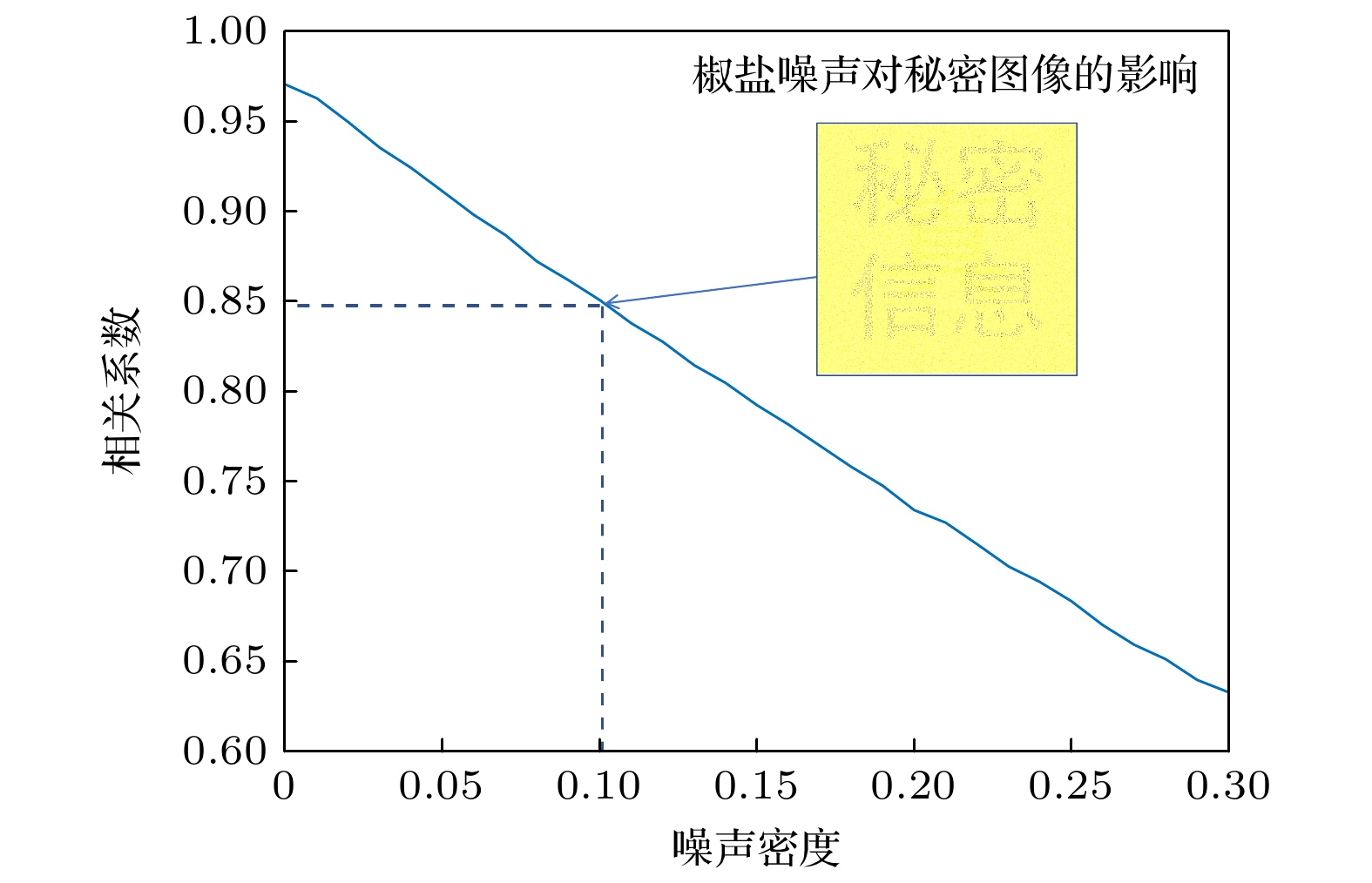
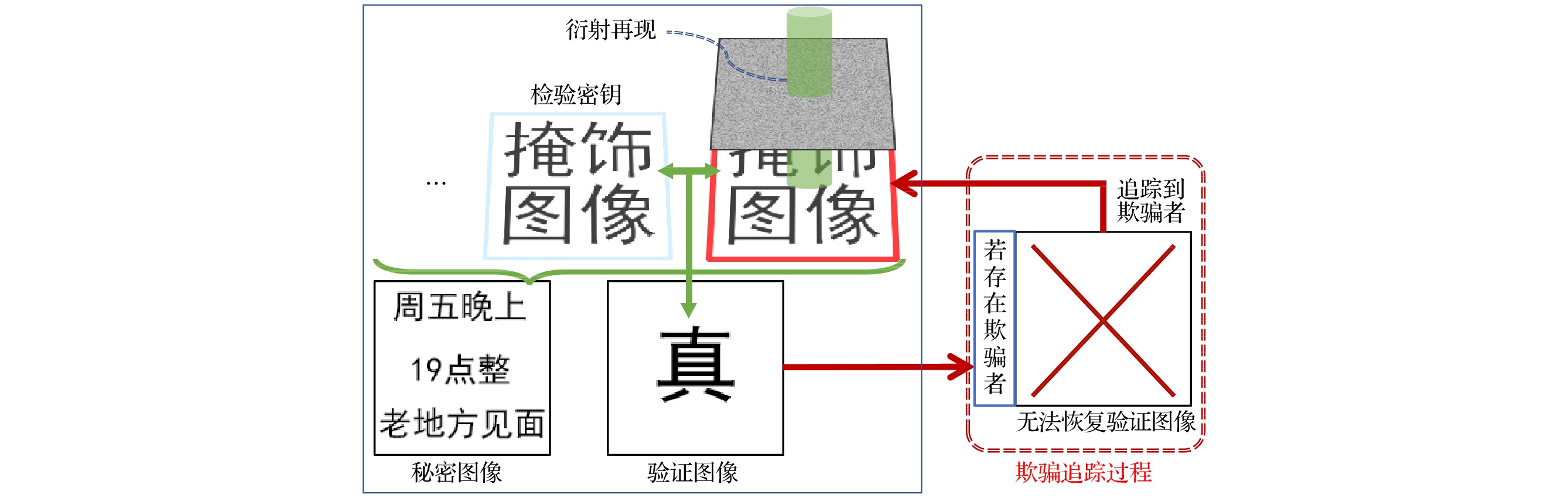
提出了一种基于光学隐藏视觉密码的欺骗追踪系统. 该系统将秘密图像分解为多幅有实际意义的掩饰图像, 将其中一张掩饰图像嵌入脆弱水印, 作为检验密钥, 检验密钥单独传输. 然后将其余掩饰图像隐藏在相位密钥中, 进行传输时有很好的不可见性. 掩饰图像的像素排列若被不诚实的参与者篡改, 则称为欺骗图像. 将每张相位密钥分发给不同的参与者, 以保证在追踪到欺骗图像时可找到对应的欺骗者. 在提取过程中, 只需要对该相位密钥进行傅里叶变换, 即可得到掩饰图像. 检验时, 将检验密钥与任一掩饰图像进行非相干叠加, 以是否出现验证图像为条件, 就可检验掩饰图像是否被篡改, 以达到欺骗追踪的目的, 将数量大于等于门限k的掩饰图像和检验密钥进行非相干叠加即可得到秘密图像, 仿真实验结果表明, 该系统可应用于利用不可见视觉密码术传递实际信息时, 对内部欺骗者的追踪.A deception tracking system based on optical hidden visual code is proposed. The system uses visual cryptography to decompose the secret image into a number of realistic masked images, which can be used to conceal the secret information. One of the masked images is embedded with a fragile watermark to ensure that it is not modified. This image serves as an inspection key to verify the other images, and the inspection key is transmitted separately. The rest of the camouflaged image is hidden in the phase key using the phase recovery algorithm, which ensures good invisibility during transmission. If the pixel arrangement of the masked image is tampered with by a dishonest participant, it is called a fraudulent image. Each phase key is distributed to different participants to ensure that the corresponding deceiver can be identified when the spoofing image is traced. In the extraction process, only the diffraction transformation of the phase key is needed to obtain the mask image. During the inspection, the inspection key is incoherently superimposed with any masked image, and the appearance of the verification image indicates whether the masked image has been tampered with, thereby achieving the purpose of deception tracking. The secret image can be obtained by incoherently superimposing the masking images, provided that the number of superimposed masking images is is greater than or equal to the threshold k, along with the inspection key. When the inspection key is superimposed with any masked image, if there is a spoofed image, no verification image will appear, and as a result, the secret image will not be restored. If there is no spoofed image, the verification image will appear, indicating that the secret image can be restored by covering all the images. The system can be used to track internal fraudsters when actual information is transmitted through invisible visual cryptography.
-
Keywords:
- optical hiding /
- visual cryptography /
- phase key /
- spoofing tracking
[1] Khan M, Shah T 2014 3D Research 5 29
 Google Scholar
Google Scholar
[2] Chen W, Javidi B, Chen X D 2014 Adv. Opt. Photonics 6 120
 Google Scholar
Google Scholar
[3] Liu S, Guo C L, Sheridan J T 2014 Opt. Laser Technol. 57 327
 Google Scholar
Google Scholar
[4] Shi Y S, Situ G H, Zhang J J 2007 Opt. Lett. 32 1914
 Google Scholar
Google Scholar
[5] Shi Y S, Situ G H, Zhang J J 2008 Opt. Lett. 33 542
 Google Scholar
Google Scholar
[6] 杨玉花, 史祎诗, 王雅丽, 肖俊, 张静娟 2011 60 034202
 Google Scholar
Google Scholar
Yang Y H, Shi Y S, Wang Y L, Xiao J, Zhang J J 2011 Acta Phys. Sin. 60 034202
 Google Scholar
Google Scholar
[7] Shi Y S, Li T, Wang Y L, Gao Q K, Zhang S G, Li H F 2013 Opt. Lett. 38 1425
 Google Scholar
Google Scholar
[8] Gao Q H, Wang Y L, Li T, Shi Y S 2014 Appl. Optics 53 4700
 Google Scholar
Google Scholar
[9] 刘祥磊, 潘泽, 王雅丽, 史祎诗 2015 64 234201
 Google Scholar
Google Scholar
Liu X L, Pan Z, Wang Y L, Shi Y S 2015 Acta Phys. Sin. 64 234201
 Google Scholar
Google Scholar
[10] Chanana A, Paulsen A, Guruswamy S, Nahata A 2016 Optica 3 1466
 Google Scholar
Google Scholar
[11] 席思星, 于娜娜, 王晓雷, 朱巧芬, 董昭, 王微, 刘秀红, 王华英 2019 68 110502
 Google Scholar
Google Scholar
Xi S X, Yu N N, Wang X L, Zhu Q F, Dong Z, Wang W, Liu X H, Wang H Y 2019 Acta Phys. Sin. 68 110502
 Google Scholar
Google Scholar
[12] 王雪光, 李明, 于娜娜, 席思星, 王晓雷, 郎利影 2019 68 240503
 Google Scholar
Google Scholar
Wang X G, Li M, Yu N N, Xi S X, Wang X L, Lang L Y 2019 Acta Phys. Sin. 68 240503
 Google Scholar
Google Scholar
[13] Machizaud J, Fournel T 2012 Opt. Express 20 22847
 Google Scholar
Google Scholar
[14] Wu H C, Chang C C 2005 Comput. Stand. Interfaces 28 123
 Google Scholar
Google Scholar
[15] Feng J B, Wu H C, Tsai C S, Chang Y F, Chu Y P 2008 Pattern Recognit. 41 3572
 Google Scholar
Google Scholar
[16] Mishra A, Gupta A 2018 J. Inf. Optim. Sci. 39 631
[17] Blundo C, Cimato S, Santis A D 2006 Theor. Comput. Sci. 369 169
 Google Scholar
Google Scholar
[18] Chen Y F, Chan Y K, Huang C C, Tsai M H, Chu Y P 2007 Inf. Sci. 177 4696
 Google Scholar
Google Scholar
[19] 于韬, 杨栋宇, 马锐, 史祎诗 2020 69 144202
 Google Scholar
Google Scholar
Yu T, Yang D Y, Ma R, Shi Y S 2020 Acta Phys. Sin. 69 144202
 Google Scholar
Google Scholar
[20] 周新隆, 祝玉鹏, 杨栋宇, 张峻浩, 卢哲, 王华英, 董昭, 柯常军, 史祎诗 2021 70 244201
 Google Scholar
Google Scholar
Zhou X L, Zhu Y P, Yang D Y, Zhang J H, Lu Z, Wang H Y, Dong Z, Ke C J, Shi Y S 2021 Acta Phys. Sin. 70 244201
 Google Scholar
Google Scholar
[21] Shi Y S, Yang X B 2017 J. Opt. 19 115703
 Google Scholar
Google Scholar
[22] Shi Y S, Yang X B 2017 Chin. Phys. Lett. 34 114204
 Google Scholar
Google Scholar
[23] Yang N, Gao Q K, Shi Y S 2018 Opt. Express 26 31995
 Google Scholar
Google Scholar
[24] Li Z F, Dong G Y, Yang D Y, Li G L, Shi Y S, Bi K, Zhou J 2019 Opt. Express 27 19212
 Google Scholar
Google Scholar
[25] 郁滨, 付正欣, 沈刚, 房礼国 2014 视觉密码 (合肥: 中国科学技术大学出版社) 第69页
Yu B, Fu Z X, Shen G, Fang L G 2014 Visual Cryptography (Vol. 1) (Hefei: University of Science and Technology of China Press) p69
-
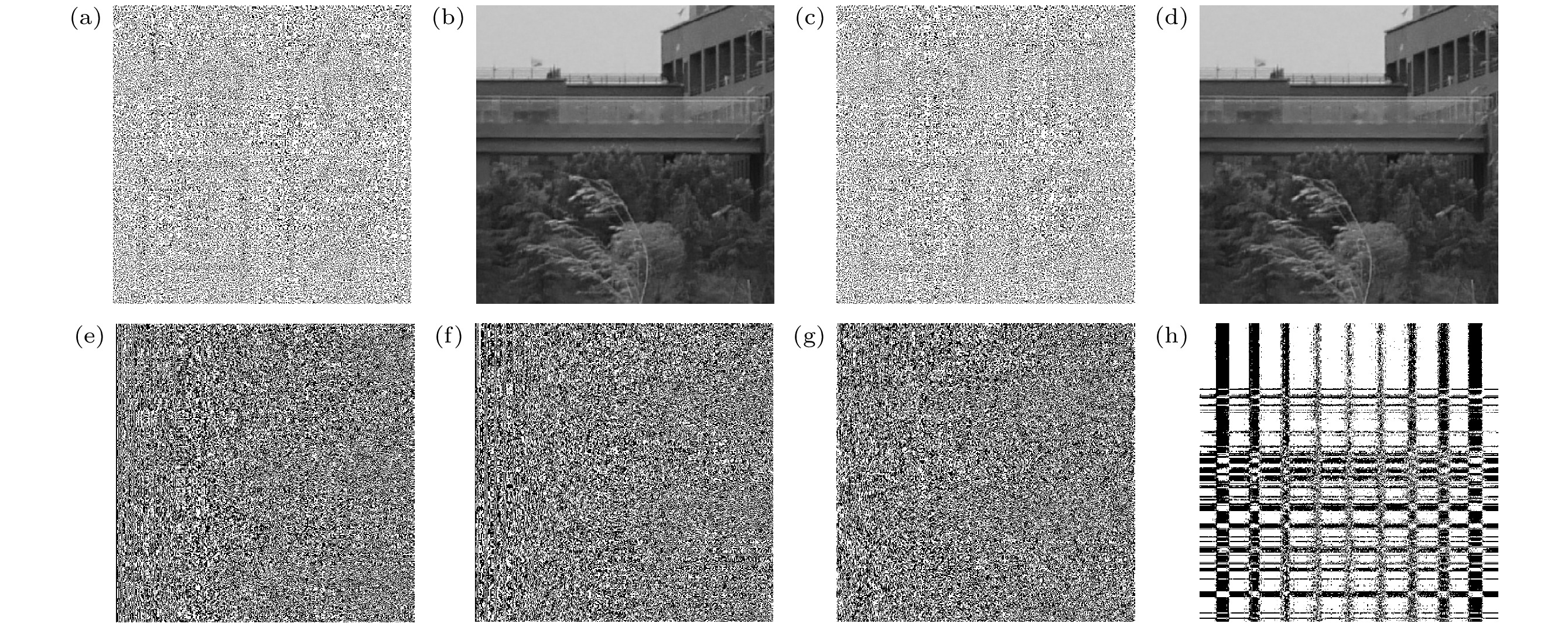
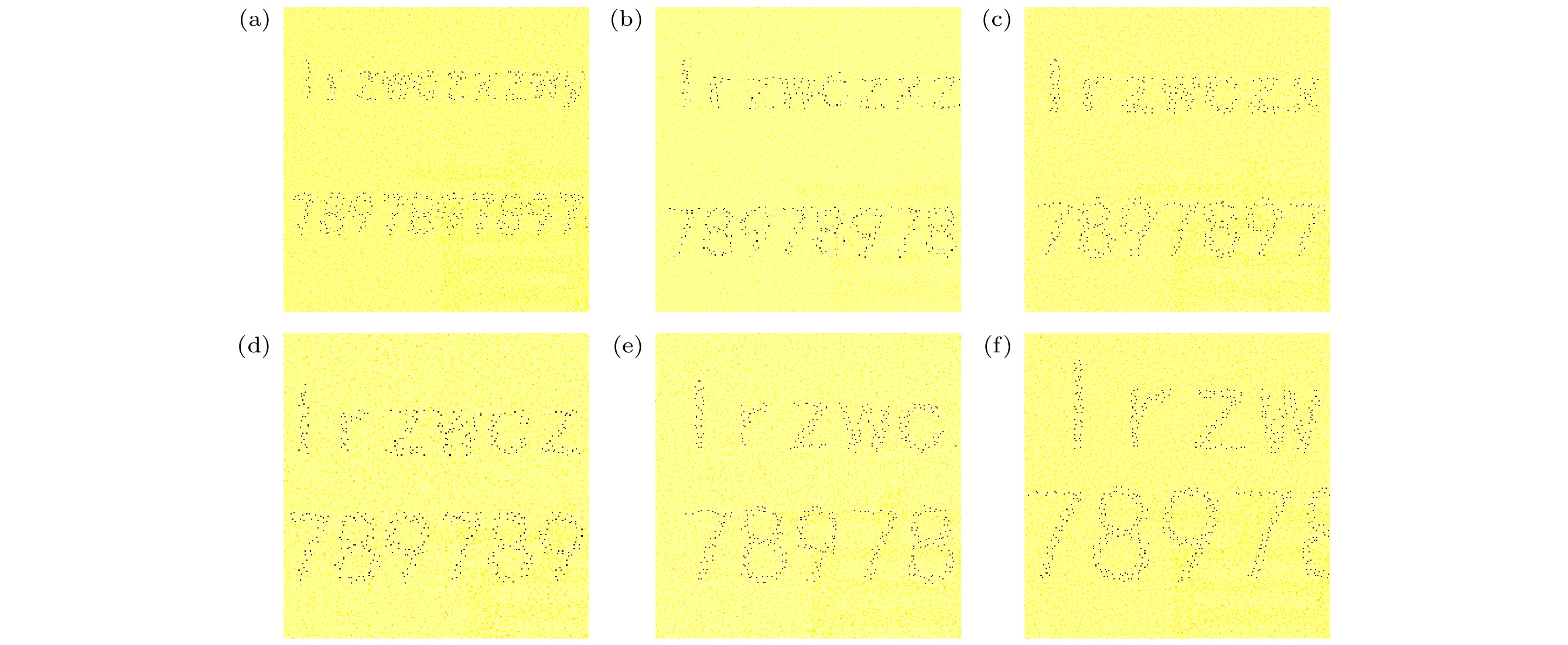
图 7 欺骗追踪过程 (a) 检验密钥; (b) 被篡改像素排列顺序的欺骗图像; (c) 从相位密钥恢复的掩饰图像; (d) 检验密钥与欺骗图像叠加结果; (e) 检验密钥与掩饰图像叠加结果; (f) 无法恢复秘密图像的结果
Fig. 7. Spoofing tracking process: (a) Test key; (b) spoofing images with altered pixel arrangement order; (c) masking image recovered from phase key; (d) test key and spoofing image superposition result; (e) test key and masking image superposition result; (f) failure to recover secret image.
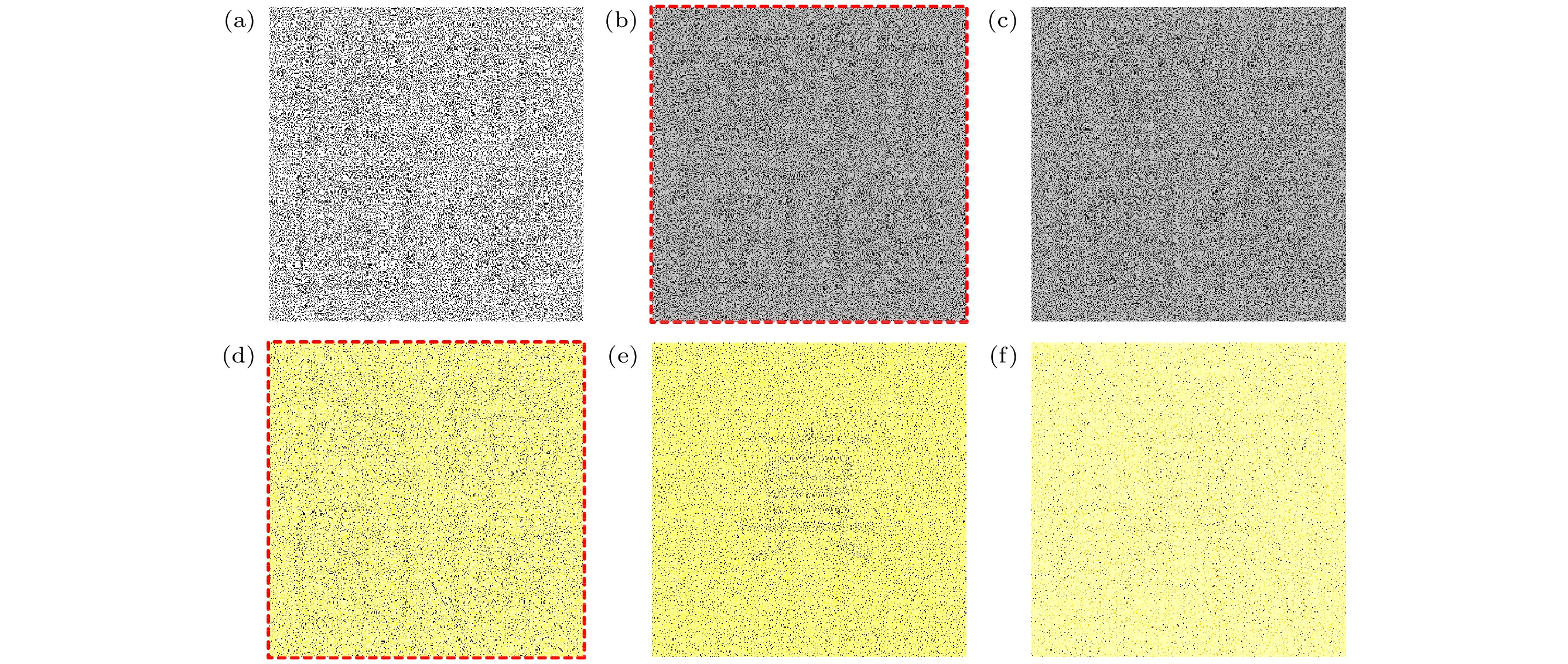
图 8 脆弱水印功能验证 (a) 宿主图像; (b) 水印图像; (c) 嵌入脆弱水印的宿主图像; (d) 提取水印图像; (e) 0.01椒盐噪声攻击提取的水印; (f) 0.01高斯噪声攻击提取的水印; (g) 图像压缩后提取的水印; (h) 10×10像素裁剪攻击后提取的水印
Fig. 8. Fragile watermarking function verification: (a) Host image; (b) watermarked image; (c) host image embedded with fragile watermark; (d) extract watermark image; (e) watermark extracted by 0.01 salt and pepper noise attack; (f) watermark extracted by 0.01 Gaussian noise attack; (g) watermark extracted after image compression; (h) watermark extracted after 10×10 pixel cropping attack.
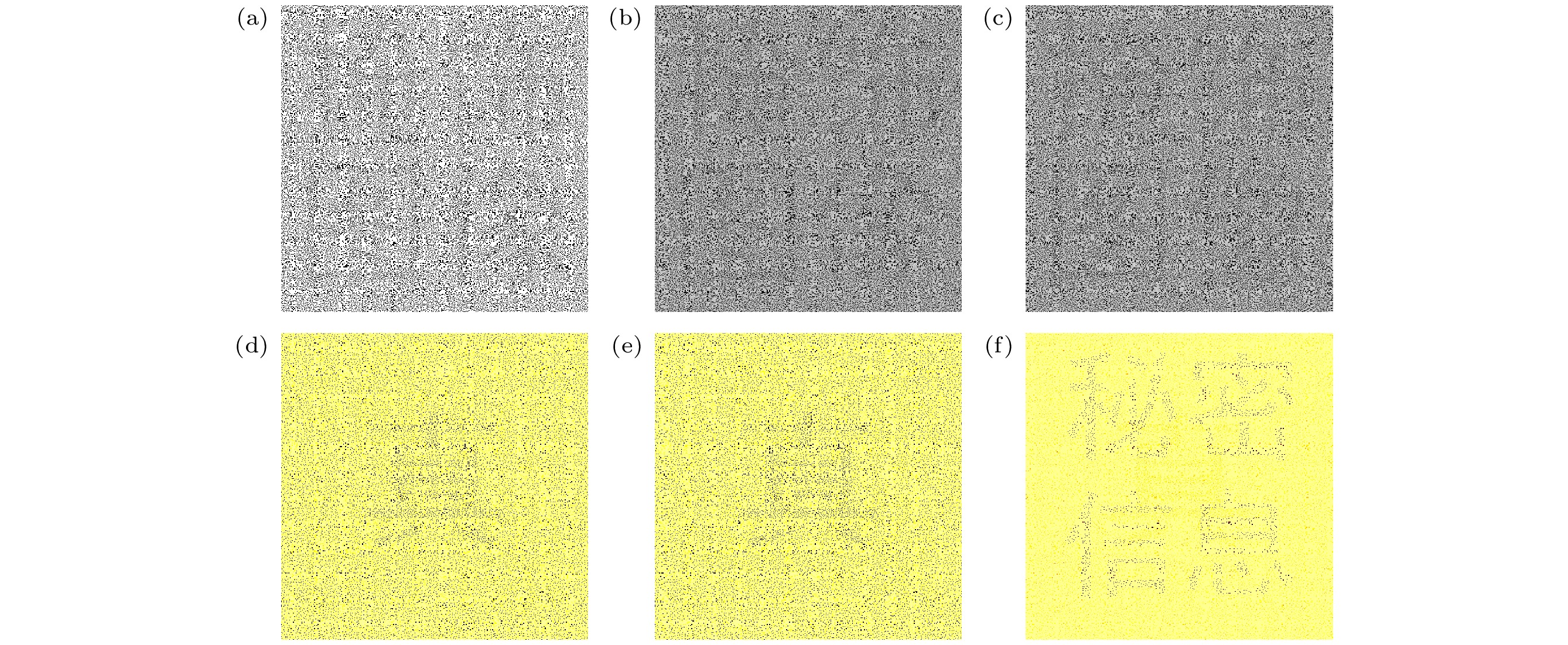
图 9 获得秘密图像的过程 (a) 检验密钥; (b)从相位密钥恢复出的掩饰图像1; (c)从相位密钥恢复出的掩饰图像2; (d) 检验密钥和掩饰图像1叠加得到的验证图像; (e) 检验密钥和掩饰图像2叠加得到的验证图像; (f) 3张图像叠加恢复的秘密图像
Fig. 9. Process of obtaining secret image: (a) Test key; (b) masking image 1 recovered from phase key; (c) masking image 2 recovered from phase key; (d) the verification image obtained by superimposing the test key and the masking image 1; (e) verification images obtained by superimposing the test key and masking image 2; (f) the secret image recovered by superimposing three images.
-
[1] Khan M, Shah T 2014 3D Research 5 29
 Google Scholar
Google Scholar
[2] Chen W, Javidi B, Chen X D 2014 Adv. Opt. Photonics 6 120
 Google Scholar
Google Scholar
[3] Liu S, Guo C L, Sheridan J T 2014 Opt. Laser Technol. 57 327
 Google Scholar
Google Scholar
[4] Shi Y S, Situ G H, Zhang J J 2007 Opt. Lett. 32 1914
 Google Scholar
Google Scholar
[5] Shi Y S, Situ G H, Zhang J J 2008 Opt. Lett. 33 542
 Google Scholar
Google Scholar
[6] 杨玉花, 史祎诗, 王雅丽, 肖俊, 张静娟 2011 60 034202
 Google Scholar
Google Scholar
Yang Y H, Shi Y S, Wang Y L, Xiao J, Zhang J J 2011 Acta Phys. Sin. 60 034202
 Google Scholar
Google Scholar
[7] Shi Y S, Li T, Wang Y L, Gao Q K, Zhang S G, Li H F 2013 Opt. Lett. 38 1425
 Google Scholar
Google Scholar
[8] Gao Q H, Wang Y L, Li T, Shi Y S 2014 Appl. Optics 53 4700
 Google Scholar
Google Scholar
[9] 刘祥磊, 潘泽, 王雅丽, 史祎诗 2015 64 234201
 Google Scholar
Google Scholar
Liu X L, Pan Z, Wang Y L, Shi Y S 2015 Acta Phys. Sin. 64 234201
 Google Scholar
Google Scholar
[10] Chanana A, Paulsen A, Guruswamy S, Nahata A 2016 Optica 3 1466
 Google Scholar
Google Scholar
[11] 席思星, 于娜娜, 王晓雷, 朱巧芬, 董昭, 王微, 刘秀红, 王华英 2019 68 110502
 Google Scholar
Google Scholar
Xi S X, Yu N N, Wang X L, Zhu Q F, Dong Z, Wang W, Liu X H, Wang H Y 2019 Acta Phys. Sin. 68 110502
 Google Scholar
Google Scholar
[12] 王雪光, 李明, 于娜娜, 席思星, 王晓雷, 郎利影 2019 68 240503
 Google Scholar
Google Scholar
Wang X G, Li M, Yu N N, Xi S X, Wang X L, Lang L Y 2019 Acta Phys. Sin. 68 240503
 Google Scholar
Google Scholar
[13] Machizaud J, Fournel T 2012 Opt. Express 20 22847
 Google Scholar
Google Scholar
[14] Wu H C, Chang C C 2005 Comput. Stand. Interfaces 28 123
 Google Scholar
Google Scholar
[15] Feng J B, Wu H C, Tsai C S, Chang Y F, Chu Y P 2008 Pattern Recognit. 41 3572
 Google Scholar
Google Scholar
[16] Mishra A, Gupta A 2018 J. Inf. Optim. Sci. 39 631
[17] Blundo C, Cimato S, Santis A D 2006 Theor. Comput. Sci. 369 169
 Google Scholar
Google Scholar
[18] Chen Y F, Chan Y K, Huang C C, Tsai M H, Chu Y P 2007 Inf. Sci. 177 4696
 Google Scholar
Google Scholar
[19] 于韬, 杨栋宇, 马锐, 史祎诗 2020 69 144202
 Google Scholar
Google Scholar
Yu T, Yang D Y, Ma R, Shi Y S 2020 Acta Phys. Sin. 69 144202
 Google Scholar
Google Scholar
[20] 周新隆, 祝玉鹏, 杨栋宇, 张峻浩, 卢哲, 王华英, 董昭, 柯常军, 史祎诗 2021 70 244201
 Google Scholar
Google Scholar
Zhou X L, Zhu Y P, Yang D Y, Zhang J H, Lu Z, Wang H Y, Dong Z, Ke C J, Shi Y S 2021 Acta Phys. Sin. 70 244201
 Google Scholar
Google Scholar
[21] Shi Y S, Yang X B 2017 J. Opt. 19 115703
 Google Scholar
Google Scholar
[22] Shi Y S, Yang X B 2017 Chin. Phys. Lett. 34 114204
 Google Scholar
Google Scholar
[23] Yang N, Gao Q K, Shi Y S 2018 Opt. Express 26 31995
 Google Scholar
Google Scholar
[24] Li Z F, Dong G Y, Yang D Y, Li G L, Shi Y S, Bi K, Zhou J 2019 Opt. Express 27 19212
 Google Scholar
Google Scholar
[25] 郁滨, 付正欣, 沈刚, 房礼国 2014 视觉密码 (合肥: 中国科学技术大学出版社) 第69页
Yu B, Fu Z X, Shen G, Fang L G 2014 Visual Cryptography (Vol. 1) (Hefei: University of Science and Technology of China Press) p69
计量
- 文章访问数: 523
- PDF下载量: 23
- 被引次数: 0












 下载:
下载: