-
测量设备无关量子密钥分发协议移除了所有测量设备的漏洞, 极大地提高了量子密钥分发系统的实际安全性, 然而, 该协议的安全密钥率相比于其他量子密钥分发协议来说仍然是较低的. 目前, 利用高维编码来提升量子密钥分发协议的性能已经在理论和实验上都得到证明, 最近有人提出了基于高维编码的测量设备无关量子密钥分发协议, 但是由于所提出的协议对实验设备性能有更高的要求, 所以在实际应用上仍然存在许多困难. 本文提出一种基于偏振和相位两种自由度的混合编码测量设备无关量子密钥分发协议, 并且利用四强度诱骗态方法分析该协议在实际条件下的安全性, 最后数值仿真结果表明, 该协议在实际条件下40 km和50 km处的最优安全码率相比于原MDI-QKD协议分别提升了52.83%和50.55%. 而且, 相比于其他基于高维编码的测量设备无关量子密钥分发协议来说, 本文提出的协议只要求本地用户拥有相位编码装置和偏振编码装置, 探测端也只需要四台单光子探测器, 这些装置都可以利用现有的实验条件实现, 说明该协议的实用价值也很高.Quantum key distribution technology refers to a method to share keys between communication parties by transmitting quantum states in public channels. Although unconditional security is the main advantage of QKD, its application prospect has been controversial in practical implementation due to the potential security risks caused by device imperfections. Fortunately, the measurement device independent quantum key distribution protocol removes the vulnerability of all measurement devices and greatly improves the practical security of the quantum key distribution system. However, the security key rate of this protocol is still lower than that of other quantum key distribution protocols. At present, using high-dimensional coding to improve the performance of the quantum key distribution protocol has been proved in theory and experiment, and recently, it has been proposed to use high-dimensional coding to improve the performance of measurement device independent quantum key distribution protocol, but because these protocols have higher requirements for the laboratory equipment performance, that the high-dimensional encoding is applied to the aforementioned protocol still has many difficulties in practical application. In this paper, we propose a hybrid coding based on the polarization and two-degree phase of freedom measurement device independent quantum key distribution protocol. In the first place in an ideal case, we introduce in detail the protocol decoding rules, then introduce 4intensity decoy-state method to solve the problem of actual light source multiphoton, in addition we also consider the statistical fluctuation effect under the condition of limited code length, channel loss, actual dark count of single photon detector and detection efficiency problem. Finally, the optimal security code rate and its corresponding optimal parameters are obtained by full parameter optimization method, And the numerical simulation results show that the security key rate of this protocol is increased by 50% by considering the practical implementation. We point out that compared with other measurement device independent quantum key distribution protocol, the proposed agreement requires local users only to have a phase encoding device and a polarization coding device, and 4 single photon detectors for detecting side. The proposed device can use the existing experimental condition, beyond that, compared with the time encoding based high dimensional measurement device independent quantum key distribution protocol, the proposed protocol possesses the advantage that the rate of system security key can be increased without increasing the repetition frequency of users. It is proved that this protocol has great application value in the future field of quantum communication, especially, in the field of quantum network communication.
-
Keywords:
- quantum key distribution /
- measurement device independent /
- high dimensional encoding /
- hyper-encoding
[1] Bennett C H, Brassard G 2014 Theor. Comput. Sci. 560 7
 Google Scholar
Google Scholar
[2] Xu F, Zhang X M, Lo H K, et al. 2019 arXiv: 1903.09051, [quant-ph]
[3] Pirandola S, Andersen U L, Banchi L, et al. 2019 arXiv: 1906.01645, [quant-ph]
[4] Lo H K, Curty M, Qi B 2012 Phys. Rev. Lett. 108 130503
 Google Scholar
Google Scholar
[5] Braunstein S L, Pirandola S 2012 Phys. Rev. Lett. 108 130502
 Google Scholar
Google Scholar
[6] Hwang W Y 2003 Phys. Rev. Lett. 91 057901
 Google Scholar
Google Scholar
[7] Wang X B 2005 Phys. Rev. Lett. 94 230503
 Google Scholar
Google Scholar
[8] Ma X, Razavi M 2012 Phys. Rev. A 86 062319
 Google Scholar
Google Scholar
[9] Tamaki K, Lo H K, Fung C H F, et al. 2012 Phys. Rev. A 85 042307
 Google Scholar
Google Scholar
[10] Wang X B 2013 Phys. Rev. A 87 012320
 Google Scholar
Google Scholar
[11] Curty M, Xu F, Cui W, et al. 2014 Nat. Commn. 5 3732
 Google Scholar
Google Scholar
[12] Xu F, Xu H, Lo H K 2014 Phys. Rev. A 89 052333
 Google Scholar
Google Scholar
[13] 杜亚男, 解文钟, 金璇, 王金东, 魏正军, 秦晓娟, 赵峰, 张智明 2015 64 110301
 Google Scholar
Google Scholar
Du YN, Xie W Z, Jin X, Wang J D, Wei Z J, Qin X J, Zhao F, Zhang Z M 2015 Acta Phys. Sin. 64 110301
 Google Scholar
Google Scholar
[14] Zhou Y H, Yu Z W, Wang X B 2016 Phys. Rev. A 93 042324
 Google Scholar
Google Scholar
[15] 于浩, 张影, 卓文合, 完颜绍澎刘金锁 2019 量子电子学报 36 450
Hao Y U, Zhang Y, Zhuo W H, Wanyan S P, Liu J S 2019 Chin. J. of Quan. Elec. 36 450
[16] 谷文苑, 赵尚弘, 东晨, 王星宇, 杨鼎 2019 68 240301
 Google Scholar
Google Scholar
Gu W Y, Zhao S H, Dong C, Wang X Y, Yang D 2019 Acta Phys. Sin. 68 240301
 Google Scholar
Google Scholar
[17] Liu Y, Chen T Y, Wang L J, et al. 2013 Phys. Rev. Lett. 111 130502
 Google Scholar
Google Scholar
[18] Rubenok A, Slater J A, Chan P, et al. 2013 Phys. Rev. Lett. 111 130501
 Google Scholar
Google Scholar
[19] Ferreira da Silva T, Vitoreti D, Xavier G B, et al. 2013 Phys. Rev. A 88 052303
 Google Scholar
Google Scholar
[20] Tang Y L, Yin H L, Chen S J, et al. 2014 Phys. Rev. Lett. 113 190501
 Google Scholar
Google Scholar
[21] Tang Z, Liao Z, Xu F, et al. 2014 Phys. Rev. Lett. 112 190503
 Google Scholar
Google Scholar
[22] Tang Y L, Yin H L, Chen S J, et al. 2015 IEEE. J. Sel. Top. Quant 21 116
 Google Scholar
Google Scholar
[23] Yin H L, Chen T Y, Yu Z W, et al. 2016 Phys. Rev. Lett. 117 190501
 Google Scholar
Google Scholar
[24] Comandar L C, Lucamarini M, Fröhlich B, et al. 2016 Nat. Photon. 10 312
 Google Scholar
Google Scholar
[25] Cozzolino D, Da Lio B, Bacco D, et al. 2019 Adv. Quantum Technol. 2 1900038
 Google Scholar
Google Scholar
[26] Ali-Khan I, Broadbent C J, Howell J C 2007 Phys. Rev. Lett. 98 060503
 Google Scholar
Google Scholar
[27] Zhang P, Aungskunsiri K, Martn-López E, et al. 2014 Phys. Rev. Lett. 112 130501
 Google Scholar
Google Scholar
[28] Lee C, Zhang Z, Steinbrecher G R, et al. 2014 Phys. Rev. A 90 062331
 Google Scholar
Google Scholar
[29] Sit A, Bouchard F, Fickler R, et al. 2017 Optica 4 1006
 Google Scholar
Google Scholar
[30] Ding Y, Bacco D, Dalgaard K, et al. 2017 NPJ Quantum Inf. 3 25
 Google Scholar
Google Scholar
[31] Dellantonio L, Sorensen A S, Bacco D 2018 Phys. Rev. A 98 062301
 Google Scholar
Google Scholar
[32] Deng F G, Ren B C, Li X H 2017 Sci. Bull. 62 46 68
[33] Wang J D, Wei Z J, Zhang H, et al. 2010 J. Phys. B: At. Mol. Opt. Phys. 43 095504
 Google Scholar
Google Scholar
[34] Mao Q P, Wang L, Zhao S M 2019 Laser Physics 29 085201
 Google Scholar
Google Scholar
[35] Cui Z X, Zhong W, Zhou L Sheng Y B 2019 Sci. China Phys. Mech. Astron. 62 110311
 Google Scholar
Google Scholar
[36] Zhou Y H, Yu Z W, Wang X B 2016 Physical Review A 93 042324
[37] Yu Z W, Zhou Y H, Wang X B 2015 Phys. Rev. A 91 032318
 Google Scholar
Google Scholar
[38] Wang Q, Wang X B 2014 Sci. Rep. 4 4612
[39] Xu F, Xu H, Lo H K 2014 Physical Review A 89 052333
[40] Xavier G B, Vilela de Faria G, Temporao G P, et al. 2008 Opt. Express 16 1867
 Google Scholar
Google Scholar
[41] Ding Y Y, Chen H, Wang S, et al. 2017 Opt. Express 25 27923
 Google Scholar
Google Scholar
[42] Ding Y Y, Chen W, Chen H, et al. 2017 Opt. Lett. 42 1023
 Google Scholar
Google Scholar
[43] Li D D, Gao S, Li G C, et al. 2018 Opt. Express 26 22793
 Google Scholar
Google Scholar
[44] Tang Y L, Yin H L, Zhao Q, et al. 2016 Phys. Rev. X 6 011024
[45] Zhang Q, Xu F H, Chen Y A, et al. 2018 Opt. Express 26 24260
 Google Scholar
Google Scholar
-
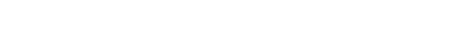
图 1 基于混和编码的MDI-QKD协议原理图. 其中, LD为光源, Pol-M, PM和IM分别为偏振调制器、相位调制器和强度调制器, DL为光延时线, BS为50:50的光分束耦合器, PBS为偏振分束器, DH和DV为单光子探测器. 首先, Alice和Bob分别通过Pol-M将偏振信息加载到光脉冲上, 然后又通过PM和IM加载时间-相位信息. Charlie将接收两者发出的光子并进行部分BSM, 然后公开其测量结果. Alice和Bob通过基比对然后利用Charlie所公开的BSM结果就能在他们原始密钥之间建立关联
Fig. 1. Schematic diagram of MDI-QKD protocol based on hyper-encoding. LD is the light source. Pol-M, PM and IM are polarization modulator, phase modulator and intensity modulator, respectively. DL is the optical delay line, BS is the 50:50 optical beam splitter, PBS is the polarization beam splitter, DH and DV are single-photon detector. First, Alice and Bob load the polarization information to the light pulse through Pol-M, respectively, and then load the phase information through PM and IM. Charlie or Eve will receive the photons emitted by both and perform part of the BSM, and then disclose their measurements. Alice and Bob can correlate their original keys by comparing the basis information and using Charlie's published BSM results.
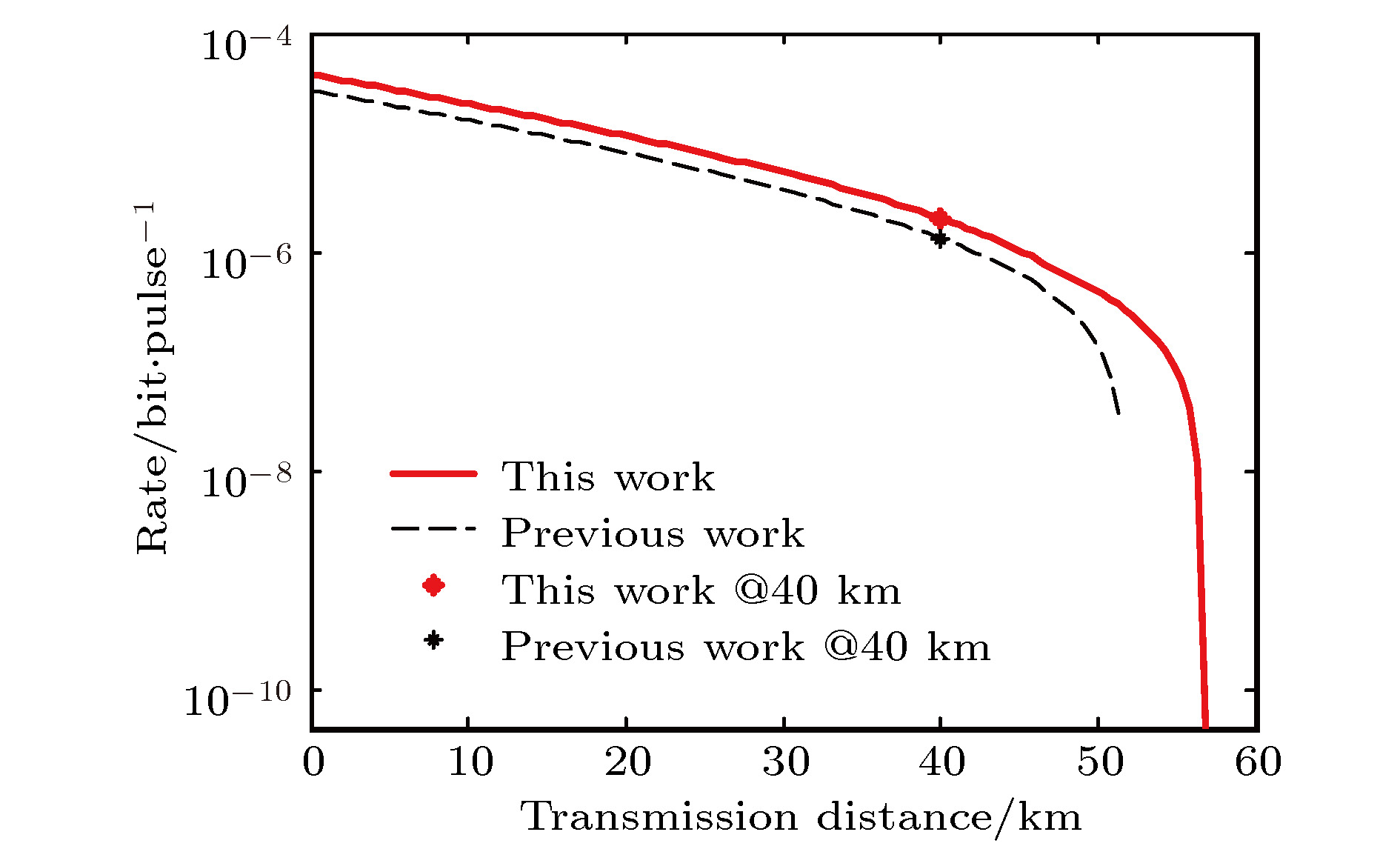
图 2 不同协议的最优安全码率比较. 这里我们利用了表6第a列的条件, 并且是以40 km处的安全码率为优化目标, 本协议的参数优化结果见表7第a列. 图中红色实线表示本协议的结果, 黑色虚线表示文献 [36]的结果
Fig. 2. Comparison of optimal security key rates for different protocols. Here, we take advantageof the conditions in column a of Table 6, and take the security key rate at 40 km as the optimizationobjective. The parameter optimization results of this protocol are shown in column a of Table 7.The solid red line in the figure represents the result of this agreement, and the dotted black linerepresents the result of Ref. [33].
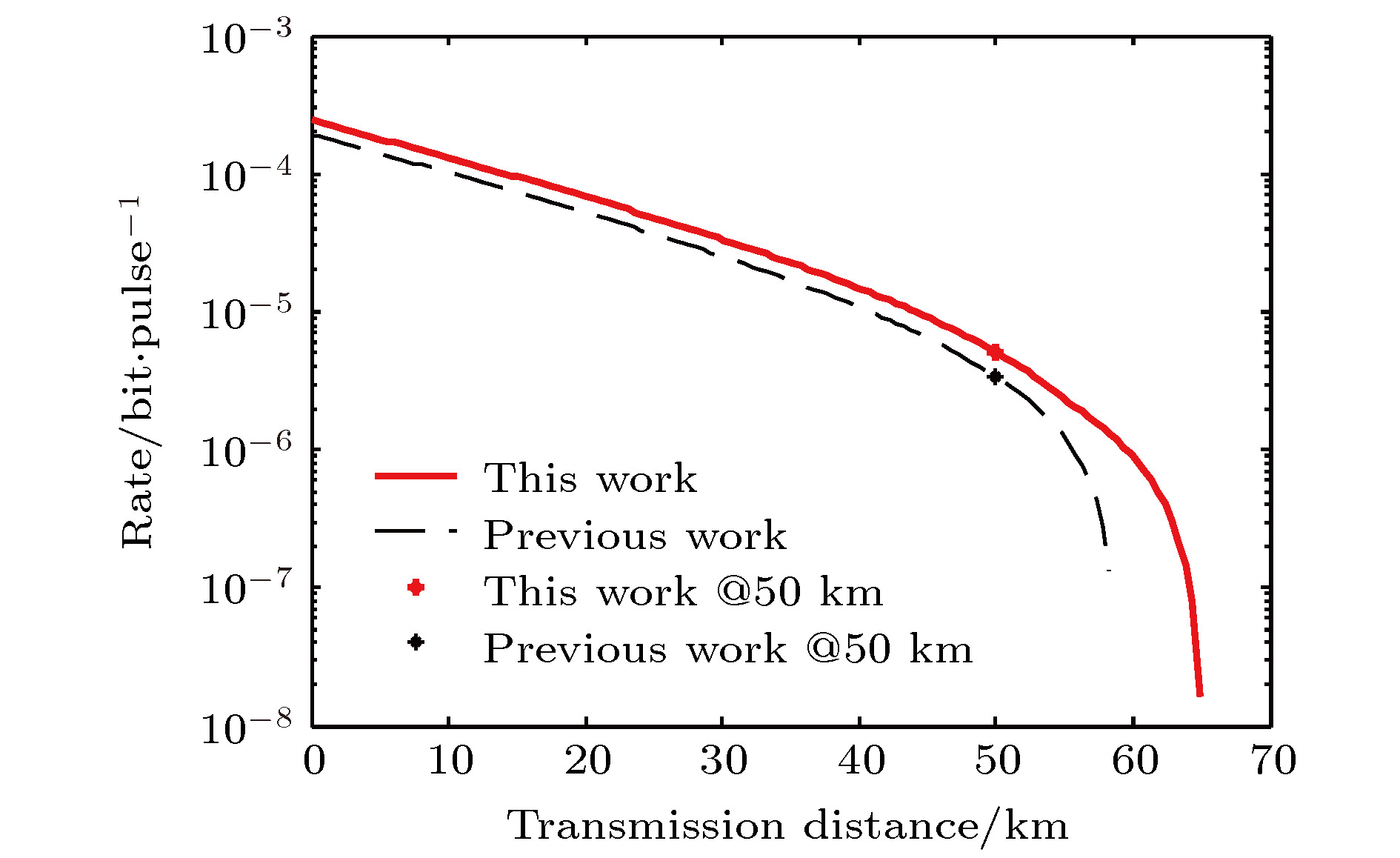
图 3 不同协议的最优安全码率比较. 这里利用了表6中第b列的条件, 并且是以50 km处的安全码率为优化目标, 本协议的参数优化结果见表7中第b列. 图中红色实线表示本协议的结果, 黑色虚线表示文献[36]的结果
Fig. 3. Comparison of optimal security key rates for different protocols. Here, we take advantage of the conditions in column b of Table 6, and take the security key rate at 50 km as the optimization objective. The parameter optimization results of this protocol are shown in column b of Table 7. The red solid line in the figure represents the result of this agreement, and the black dotted line represents the result of Ref. [36].
表 1 当相位比特在X基中选择时, 本协议单光子干涉的第3类和第4类情况的BSM结果比较
Table 1. BSM results for class 3 and class 4 cases of single-photon interference in this protocol are compared when phase bits are selected in the X basis.
Alice & Bob $ {\theta }_{\mathrm{a}}-{\theta }_{\mathrm{b}} $ $0$ $ \pm {\text{π}}$ $j = k$且$j, k \in X$ A0, B0 A1, B1 $j \ne k$且$j, k \in X$ A0, B1 A1, B0 表 2 本协议的解码规则, 其中flip表示比特翻转, No flip表示比特相同, C0表示事件{在r时刻和s时刻分别有且只有一个探测器响应}, 0表示没有成功事件
Table 2. The decoding rules of this protocol, where flip represents the bit flip, No flip represents the same bit, C0 represents the event {there is only one detector response at time r and time s respectively}, and 0 indicates that no success event occurred.
偏振基 相位基 $l, m \in Z$ $l, m \in X$ 相位基不匹配 Flip No flip Flip No flip Flip No flip $j, k \in Z$ C0, D1, D2,
D3, D40 A0, B0, B1, D1,
D2, D3, D4A1 D1, D2,
D3, D40 $j, k \in X$ C0, D2, D3 D1, D4 A0, D2, D3, B0
$(j = k)$
B1$(j \ne k)$A1, D1, D4, B0
$(j \ne k)$
B1$(j = k)$D2, D3 D1, D4 偏振基不匹配 C0 0 A0 A1 0 0 表 3 本协议不同情况下可能获得的比特信息及其相应的概率. 其中Ph (Po)-z (x)表示获取以Z(X)基编码的Ph-bits(Po-bits)信息
Table 3. The bitwise information that may be obtained under different circumstances in this agreement and its corresponding probability. Where Ph(Po)-z(x) represents the Ph-bits (Po-bits) information encoded by z (x) basis.
偏振基 相位基 $l, m \in Z$ $l, m \in X$ 相位基不匹配 $l = m$ $l \ne m$ 单光子干涉 双光子干涉 $j, k \in Z$ $j = k$ 0 1 Ph-z 1 Ph-x 0 0 $j \ne k$ 1 Po-z 1 Ph-z 1 Po-z 1 Po-z 1/2 Po-z $j, k \in X$ $j = k$ 1/2 Po-x 1 Ph-z 1 Ph-x 1/2 Po-x 1/4 Po-x $j \ne k$ 1/2 Po-x 1 Ph-z 1 Ph-x 1/2 Po-x 1/4 Po-x 偏振基不匹配 0 1 Ph-z 1/2 Ph-x 0 0 表 4 本协议的诱骗态方案以及不同强度光源所获得的比特信息. 其中Po-X(Z)和Ph-Z(X)分别表示加载信息时偏振基选择Z(X)基和相位基选择Z(X)基,
${p_x}, {p_y}, {p_z}$ 分别表示三种强度光源的概率, 分数表示获得比特信息的概率, z(x)-ph(po)表示该信息是用相位(偏振)解码方式获得的z(x)基下的比特信息Table 4. The scheme of decoy state and the bit information obtained by different intensity light sources. Where, Po-X (Z) and Ph-Z (X) respectively represent the polarization basis selection Z(X) basis and phase basis selection Z(X) basis when loading information,
${p_x}, {p_y}, {p_z}$ respectively represent the probability of three intensity light sources, fraction represents the probability of obtaining bit information, and z(x) -ph(Po) represents the bit information under z(x) basis obtained by phase (polarization) decoding.Bob Alice Po-Z Po-X Ph-Z Ph-X Ph-Z Ph-X ${p_z}$ $1/2{p_y}$ $1/2{p_y}$ ${p_x}$ Po-Z Ph-Z ${p_z}$ 1/4 z-po
1/2 z-ph1/4 z-po 1/2 z-ph 0 Ph-X $1/2{p_y}$ 1/4 z-po 1/4 x-ph
1/2 z-po0 1/4 x-ph Po-X Ph-Z $1/2{p_y}$ 1/2 z-ph 0 1/4 x-po
1/2 z-ph1/4 x-po Ph-X ${p_x}$ 0 1/4 x-ph 1/4 x-po 1/4 x-po
1/2 x-ph表 5 本协议的诱骗态方法获得的比特信息. 其中x, y, z分别表示三种强度的光源, Ph和Po分别表示相位比特和偏振比特, 数字表示获得比特信息的概率, z和x表示获得信息所属的基
Table 5. The bit information obtained by the decoy state method of this protocol. Where x, y and z represent the light source of three kinds of intensity, Ph and Po respectively represent phase bit and polarization bit, fraction represents the probability of obtaining bit information, and z and x represent the basis to which the obtained information belongs.
Bob Alice z y x Ph Po Ph Po Ph Po z 1/2 z 1/4 z 1/4 z 1/8 z 0 0 y 1/4 z 1/8 z 1/8 z
1/16 x1/8 z
1/16 x1/8 x 1/8 x x 0 0 1/8 x 1/8 x 1/2 x 1/4 x 表 7 本协议两种条件下的参数优化结果.
Table 7. Parameter optimization results under the two conditions of this agreement.
L / km ${\mu _x}$ ${\mu _y}$ ${\mu _z}$ ${p_x}$ ${p_y}$ ${p_z}$ a 40 0.0601 0.2907 0.2992 0.4636 0.0310 0.4009 b 50 0.0659 0.3200 0.2744 0.5212 0.0351 0.3283 表 6 数值模拟相关参数.
${e_0}$ 是当Alice或Bob发送空脉冲时的误码率;${e_{\rm{d}}}$ 为参考系对准误差;${p_{\rm{d}}}$ 为暗计数率;${\eta _{\rm{d}}}$ 为探测效率;${f_{\rm{e}}}$ 为误码纠错效率; N为每个发送端发送的光脉冲总数Table 6. Relevant parameters of numerical simulation.
${e_0}$ is the bit error rate when Alice or Bob sends an empty pulse;${e_{\rm{d}}}$ is the reference system alignment error;${p_{\rm{d}}}$ is the dark count rate;${\eta _{\rm{d}}}$ is the detection efficiency;${f_{\rm{e}}}$ is the error code correction efficiency; N is the the total number of light pulses sent by each sender.${e_0}$ ${e_{\rm{d}}}$/% ${p_{\rm{d}}}$ ${\eta _{\rm{d}}}$/% ${f_{\rm{e}}}$ N $\epsilon $ a 0.5 1.5 $6.02 \times {10^{ - 6}}$ 14.5 1.16 ${10^{10}}$ ${10^{{\rm{ - }}7}}$ b 0.5 1.5 ${10^{ - 7}}$ 40 1.16 ${10^9}$ ${10^{{\rm{ - }}7}}$ 表 8 最优安全码率的比较.
${R_{\rm{p}}}$ 和${R_{\rm{t}}}$ 分别表示文献[36]中的工作和本工作在不同条件下的计算结果. Improvement表示${R_{\rm{t}}}$ 相对于${R_{\rm{p}}}$ 提升的比例Table 8. Comparison of optimal security key rates.
${R_{\rm{p}}}$ and${R_{\rm{t}}}$ respectively represent the calculation results of the work in Ref. [36] and this work under different conditions. Improvement is the ratio of${R_{\rm{t}}}$ to${R_{\rm{p}}}$ .L / km ${R_{\rm{p}}}$ ${R_{\rm{t}}}$ Improvement/% a 40 $1.3394 \times {10^{ - 6}}$ $2.047 \times {10^{ - 6}}$ 52.83 b 50 $3.3983 \times {10^{ - 6}}$ $5.116 \times {10^{ - 6}}$ 50.55 -
[1] Bennett C H, Brassard G 2014 Theor. Comput. Sci. 560 7
 Google Scholar
Google Scholar
[2] Xu F, Zhang X M, Lo H K, et al. 2019 arXiv: 1903.09051, [quant-ph]
[3] Pirandola S, Andersen U L, Banchi L, et al. 2019 arXiv: 1906.01645, [quant-ph]
[4] Lo H K, Curty M, Qi B 2012 Phys. Rev. Lett. 108 130503
 Google Scholar
Google Scholar
[5] Braunstein S L, Pirandola S 2012 Phys. Rev. Lett. 108 130502
 Google Scholar
Google Scholar
[6] Hwang W Y 2003 Phys. Rev. Lett. 91 057901
 Google Scholar
Google Scholar
[7] Wang X B 2005 Phys. Rev. Lett. 94 230503
 Google Scholar
Google Scholar
[8] Ma X, Razavi M 2012 Phys. Rev. A 86 062319
 Google Scholar
Google Scholar
[9] Tamaki K, Lo H K, Fung C H F, et al. 2012 Phys. Rev. A 85 042307
 Google Scholar
Google Scholar
[10] Wang X B 2013 Phys. Rev. A 87 012320
 Google Scholar
Google Scholar
[11] Curty M, Xu F, Cui W, et al. 2014 Nat. Commn. 5 3732
 Google Scholar
Google Scholar
[12] Xu F, Xu H, Lo H K 2014 Phys. Rev. A 89 052333
 Google Scholar
Google Scholar
[13] 杜亚男, 解文钟, 金璇, 王金东, 魏正军, 秦晓娟, 赵峰, 张智明 2015 64 110301
 Google Scholar
Google Scholar
Du YN, Xie W Z, Jin X, Wang J D, Wei Z J, Qin X J, Zhao F, Zhang Z M 2015 Acta Phys. Sin. 64 110301
 Google Scholar
Google Scholar
[14] Zhou Y H, Yu Z W, Wang X B 2016 Phys. Rev. A 93 042324
 Google Scholar
Google Scholar
[15] 于浩, 张影, 卓文合, 完颜绍澎刘金锁 2019 量子电子学报 36 450
Hao Y U, Zhang Y, Zhuo W H, Wanyan S P, Liu J S 2019 Chin. J. of Quan. Elec. 36 450
[16] 谷文苑, 赵尚弘, 东晨, 王星宇, 杨鼎 2019 68 240301
 Google Scholar
Google Scholar
Gu W Y, Zhao S H, Dong C, Wang X Y, Yang D 2019 Acta Phys. Sin. 68 240301
 Google Scholar
Google Scholar
[17] Liu Y, Chen T Y, Wang L J, et al. 2013 Phys. Rev. Lett. 111 130502
 Google Scholar
Google Scholar
[18] Rubenok A, Slater J A, Chan P, et al. 2013 Phys. Rev. Lett. 111 130501
 Google Scholar
Google Scholar
[19] Ferreira da Silva T, Vitoreti D, Xavier G B, et al. 2013 Phys. Rev. A 88 052303
 Google Scholar
Google Scholar
[20] Tang Y L, Yin H L, Chen S J, et al. 2014 Phys. Rev. Lett. 113 190501
 Google Scholar
Google Scholar
[21] Tang Z, Liao Z, Xu F, et al. 2014 Phys. Rev. Lett. 112 190503
 Google Scholar
Google Scholar
[22] Tang Y L, Yin H L, Chen S J, et al. 2015 IEEE. J. Sel. Top. Quant 21 116
 Google Scholar
Google Scholar
[23] Yin H L, Chen T Y, Yu Z W, et al. 2016 Phys. Rev. Lett. 117 190501
 Google Scholar
Google Scholar
[24] Comandar L C, Lucamarini M, Fröhlich B, et al. 2016 Nat. Photon. 10 312
 Google Scholar
Google Scholar
[25] Cozzolino D, Da Lio B, Bacco D, et al. 2019 Adv. Quantum Technol. 2 1900038
 Google Scholar
Google Scholar
[26] Ali-Khan I, Broadbent C J, Howell J C 2007 Phys. Rev. Lett. 98 060503
 Google Scholar
Google Scholar
[27] Zhang P, Aungskunsiri K, Martn-López E, et al. 2014 Phys. Rev. Lett. 112 130501
 Google Scholar
Google Scholar
[28] Lee C, Zhang Z, Steinbrecher G R, et al. 2014 Phys. Rev. A 90 062331
 Google Scholar
Google Scholar
[29] Sit A, Bouchard F, Fickler R, et al. 2017 Optica 4 1006
 Google Scholar
Google Scholar
[30] Ding Y, Bacco D, Dalgaard K, et al. 2017 NPJ Quantum Inf. 3 25
 Google Scholar
Google Scholar
[31] Dellantonio L, Sorensen A S, Bacco D 2018 Phys. Rev. A 98 062301
 Google Scholar
Google Scholar
[32] Deng F G, Ren B C, Li X H 2017 Sci. Bull. 62 46 68
[33] Wang J D, Wei Z J, Zhang H, et al. 2010 J. Phys. B: At. Mol. Opt. Phys. 43 095504
 Google Scholar
Google Scholar
[34] Mao Q P, Wang L, Zhao S M 2019 Laser Physics 29 085201
 Google Scholar
Google Scholar
[35] Cui Z X, Zhong W, Zhou L Sheng Y B 2019 Sci. China Phys. Mech. Astron. 62 110311
 Google Scholar
Google Scholar
[36] Zhou Y H, Yu Z W, Wang X B 2016 Physical Review A 93 042324
[37] Yu Z W, Zhou Y H, Wang X B 2015 Phys. Rev. A 91 032318
 Google Scholar
Google Scholar
[38] Wang Q, Wang X B 2014 Sci. Rep. 4 4612
[39] Xu F, Xu H, Lo H K 2014 Physical Review A 89 052333
[40] Xavier G B, Vilela de Faria G, Temporao G P, et al. 2008 Opt. Express 16 1867
 Google Scholar
Google Scholar
[41] Ding Y Y, Chen H, Wang S, et al. 2017 Opt. Express 25 27923
 Google Scholar
Google Scholar
[42] Ding Y Y, Chen W, Chen H, et al. 2017 Opt. Lett. 42 1023
 Google Scholar
Google Scholar
[43] Li D D, Gao S, Li G C, et al. 2018 Opt. Express 26 22793
 Google Scholar
Google Scholar
[44] Tang Y L, Yin H L, Zhao Q, et al. 2016 Phys. Rev. X 6 011024
[45] Zhang Q, Xu F H, Chen Y A, et al. 2018 Opt. Express 26 24260
 Google Scholar
Google Scholar
计量
- 文章访问数: 8467
- PDF下载量: 113
- 被引次数: 0












 下载:
下载: