-
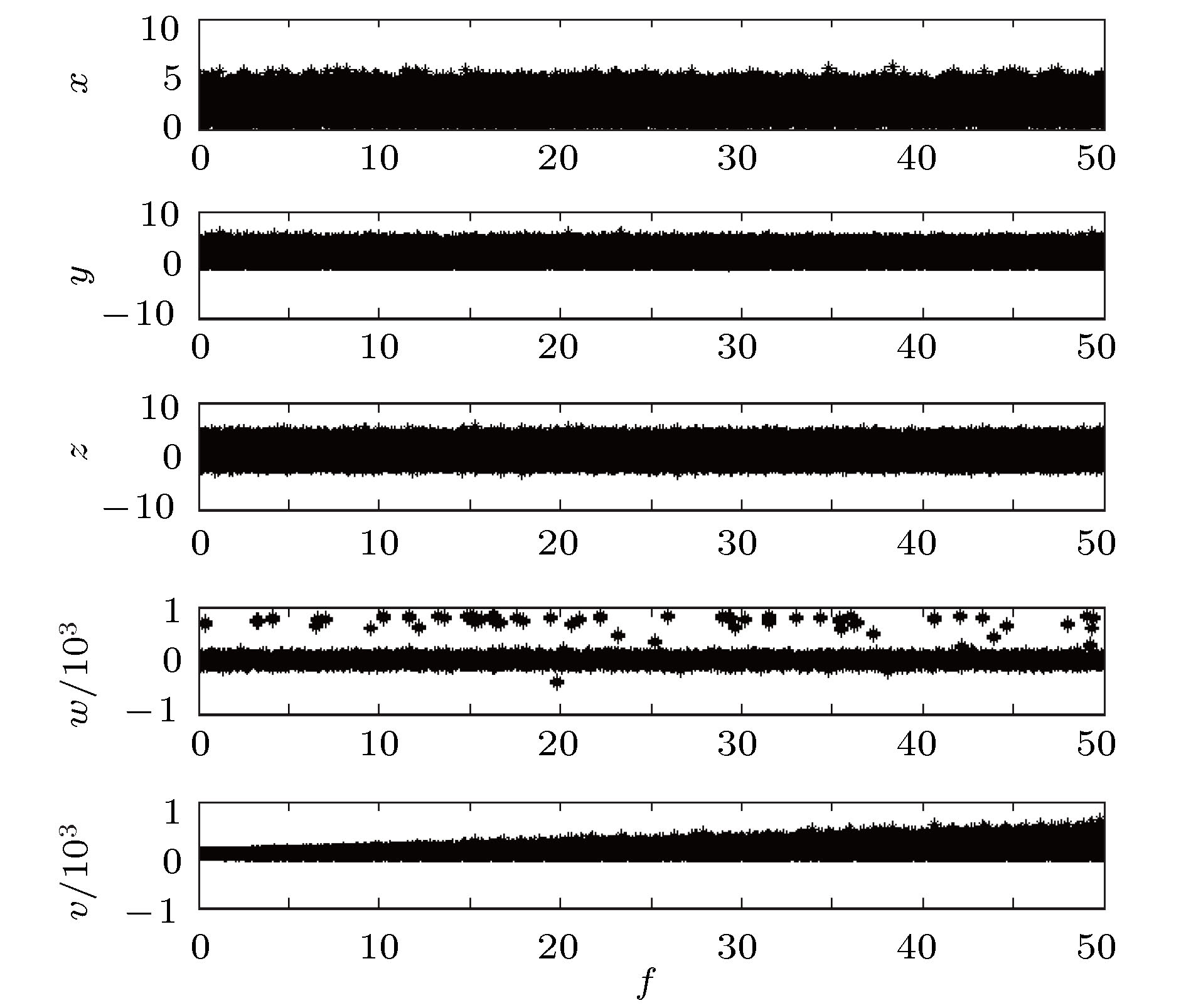
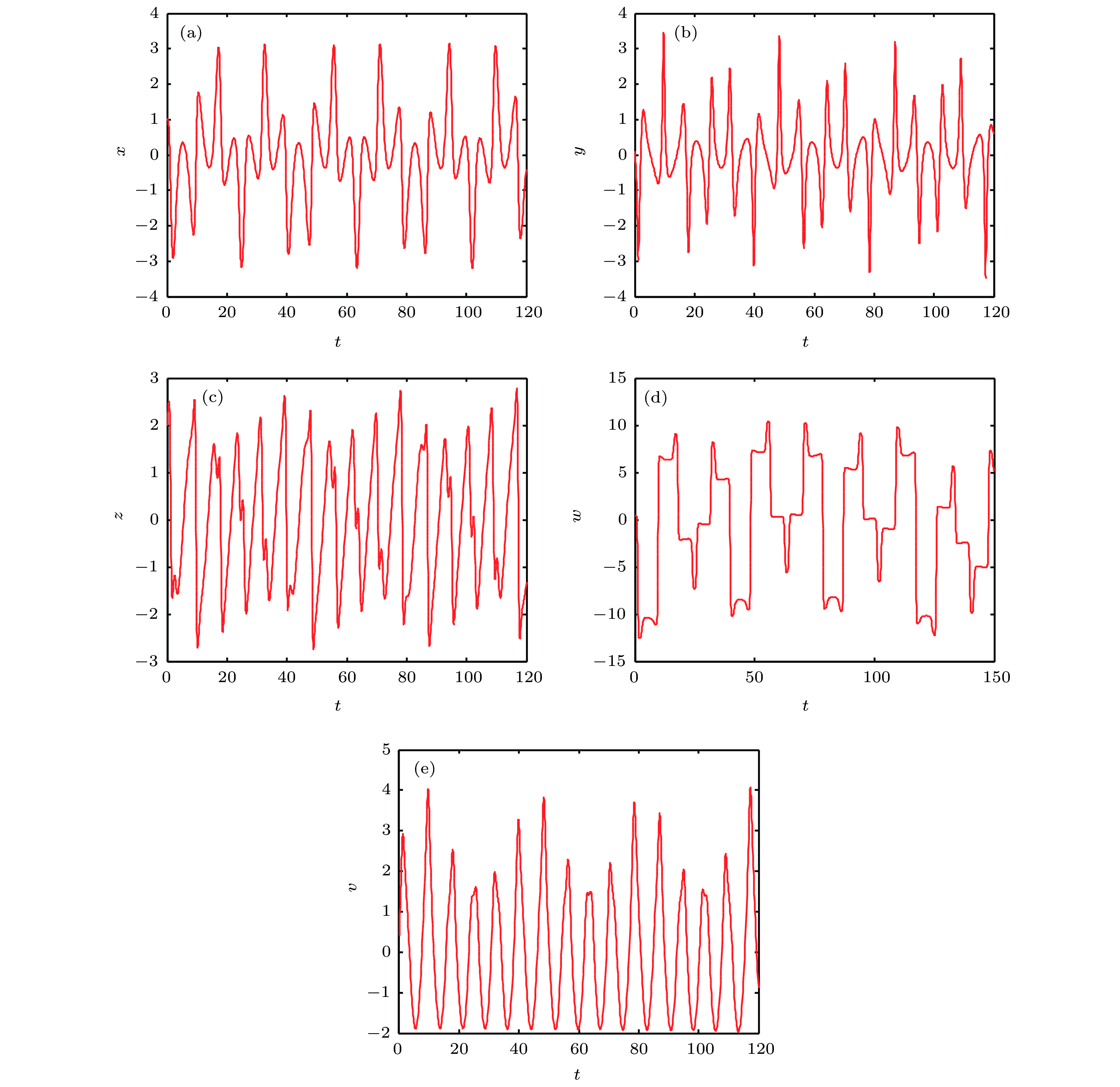
本文提出了一种基于新的五维多环多翼超混沌系统的数字图像加密方法. 首先, 将明文图像矩阵和五条混沌序列分别通过QR分解法分解成一个正交矩阵和一个上三角矩阵, 将混沌系统产生的五条混沌序列分别通过LU分解法分解成一个上三角矩阵和一个下三角矩阵, 分别将两个上三角矩阵和一个下三角矩阵相加, 得到五个离散后的混沌序列; 其次, 将明文图像矩阵分解出来的正交矩阵与五个混沌序列分解出来的五个正交矩阵相乘, 同时把明文图像矩阵分解出来的上三角矩阵中的元素通过混沌序列进行位置乱, 再将操作后的两个矩阵相乘; 最后, 将相乘后的矩阵通过混沌序列进行比特位位置乱, 再用混沌序列与其进行按位“异或”运算, 得到最终加密图像. 理论分析和仿真实验结果表明该算法的密钥空间远大于10200, 密钥敏感性强, 能够有效地抵御统计分析和灰度值分析的攻击, 对数字图像的加密具有很好的加密效果.The complex structure of hyperchaos and its complex dynamic behavior have a good application prospect in the fields of image encryption, digital watermarking and information security. Therefore, it has become very important to generate chaotic attractors with multi-vortex and multi-winged multi-rings with complex topologies. In this paper, we propose a new five-dimensional hyperchaotic system capable of generating multi-ring and multi-wing, and carry out theoretical analysis and numerical simulation experiments on some basic dynamic characteristics of the chaotic system. Such as equilibrium point, dissipation, Lyapunov exponent, bifurcation diagram, phase diagram and so on. In the process of encryption, first, we decompose the plaintext image matrix and the five chaotic sequences into an orthogonal matrix and an upper triangular matrix by QR decomposition. The five chaotic sequences generated by the chaotic system are respectively decomposed into an upper triangular matrix and a lower triangular matrix by the LU decomposition method. The upper triangular matrix decomposed by the QR decomposition method and the lower triangular matrix decomposed by the LU decomposition method are respectively added to obtain five discrete chaotic sequences. At the same time, the five discrete chaotic sequences are added to the upper triangular matrix decomposed by the LU decomposition method to obtain the final five discrete chaotic sequences. Secondly, the orthogonal matrix decomposed by the plaintext image matrix is multiplied by five orthogonal matrices decomposed by five chaotic sequences. At the same time, the elements in the upper triangular matrix decomposed by the plaintext image matrix are chaotically arranged by the chaotic sequence, and then the two matrices after the operation are multiplied. Finally, the multiplied matrix is chaotically placed on the bit by a chaotic sequence. Then use the chaotic sequence to perform a bitwise XOR operation to obtain the final encrypted image. The theoretical analysis and simulation results show that the algorithm has large key space and strong key sensitivity. It can effectively resist the attacks of statistical analysis and gray value analysis, and has good encryption effect on digital image encryption. This image encryption algorithm using a combination of conventional encryption and chaotic encryption does not have a defined plaintext ciphertext mapping relationship.
-
Keywords:
- five-dimensional hyperchaotic system /
- orthogonal decomposition /
- bit disturb /
- digital image encryption
[1] 王平, 冯勇, 孙黎霞, 韩凤玲 2002 控制理论与应用 21 1
 Google Scholar
Google Scholar
Wang P, Feng Y, Sun L X, Han F L 2002 Control Theory & Appl. 21 1
 Google Scholar
Google Scholar
[2] 禹思敏 2005 54 1500
 Google Scholar
Google Scholar
Yu S M 2005 Acta Phys.Sin. 54 1500
 Google Scholar
Google Scholar
[3] Karthikeyan R, Serdar C, Peiman N, Abdul J M, Sajad J, Anitha K 2018 Eur. Phys. J. Plus 133 354
 Google Scholar
Google Scholar
[4] 贾美美, 蒋浩刚, 李文静 2019 68 130503
 Google Scholar
Google Scholar
Jia M M, Jiang H G, Li W J 2019 Acta Phys. Sin. 68 130503
 Google Scholar
Google Scholar
[5] Li Y X, Tang W K S, Chen G R 2005 Int. J. Bifurcation Chaos. 15 3367
 Google Scholar
Google Scholar
[6] 彭再平, 王春华, 林愿, 骆小文 2014 63 240506
 Google Scholar
Google Scholar
Peng Z P, Wang C H, Lin Y, Luo X W 2014 Acta Phys. Sin. 63 240506
 Google Scholar
Google Scholar
[7] 刘杨 2015 博士学位论文 (哈尔滨: 哈尔滨工业大学)
Liu Y 2015 Ph. D. Dissertation (Harbin: Harbin Institute of Technology) (in Chinese)
[8] 禹思敏 2018 新型混沌电路与系统的设计原理及其应用 (北京: 科学出版社) 第139—155页
Yu S M 2018 Design Principles and Applications of New Chaotic Circuits and Systems (Beijing: Science Press) pp139– 155 (in Chinese)
[9] Zhang L H, Liao X F, Wang X B 2005 Chaos, Solitons Fractals 24 759
 Google Scholar
Google Scholar
[10] Wong K, Kwor B, Law W 2008 Phys. Lett. A 372 2645
 Google Scholar
Google Scholar
[11] Zhang W, Yu H, Zhao Y L, Zhu Z L 2016 Signal Process. 118 36
 Google Scholar
Google Scholar
[12] Luo Y L, Zhou R L, Liu J X, Gao Y, Ding X M 2018 Nonlinear Dyn. 4 1
[13] Ye G D, Pan C, Huang X L, Mei Q X 2018 Nonlinear Dyn. 20 18
[14] Abanda Y, Tiedeu A 2016 IET Image Proc. 10 742
 Google Scholar
Google Scholar
[15] Zhang Y 2018 Inf. Sci. 255 31145
[16] He Y, Zhang Y Q, Wang X Y 2018 Neural Comput. Appl. 10 1
[17] Raza S F, Satpute V 2018 Nonlinear Dyn. 254 1
[18] Ahmad J, Khan M A, Hwang S O, Khan J S 2017 Neural Comput. Appl. 28 953
[19] Ahmad J, Khan M A, Ahmed F, Khan J S 2018 Neural Comput. Appl. 3 1
[20] Sprott J C 1994 Phys. Rev. E 50 647
 Google Scholar
Google Scholar
[21] Enayatifar R, Abdullah A H, Isnin I F, Altameem A, Lee A 2017 Opt. Lasers Eng. 90 146
 Google Scholar
Google Scholar
[22] Liu H J, Wang X Y, Kadir A 2012 Appl. Soft Comput. 12 1457
 Google Scholar
Google Scholar
-
图 4 三维相图 (a)
$x \text- y \text- z$ 三维图; (b)$x \text- y \text- w$ 三维图; (c)$x \text- y \text- v$ 三维图; (d)$x \text- z \text- w$ 三维图; (e)$x \text- z \text- v$ 三维图; (f)$x \text- w \text- v$ 三维图; (g)$y \text- z \text- w$ 三维图; (h)$y \text- z \text- v$ 三维图; (i)$y \text- w \text- v$ 三维图; (j)$z \text- w \text- v$ 三维图Fig. 4. Three-dimensional phase diagram: (a)
$x \text- y \text- z$ Three-dimensional map; (b)$x \text- y \text- w$ Three-dimensional map; (c)$x \text- y \text- v$ Three-dimensional map; (d)$x \text- z \text- w$ Three-dimensional map; (e)$x \text- z \text- v$ Three-dimensional map; (f)$x \text- w \text- v$ Three-dimensional map; (g)$y \text- z \text- w$ Three-dimensional map; (h)$y \text- z \text- v$ Three-dimensional map; (i)$x \text- y \text- z$ Three-dimensional map; (j)$z \text- w \text- v$ Three-dimensional map.图 5 二维平面相图 (a)
$x \text- y$ 平面; (b)$x \text- z$ 平面; (c)$x \text- v$ 平面; (d)$y \text- z$ 平面; (e)$y \text- w$ 平面; (f)$z \text- w$ 平面; (g)$z \text- v$ 平面Fig. 5. Two-dimensional plane phase diagram: (a)
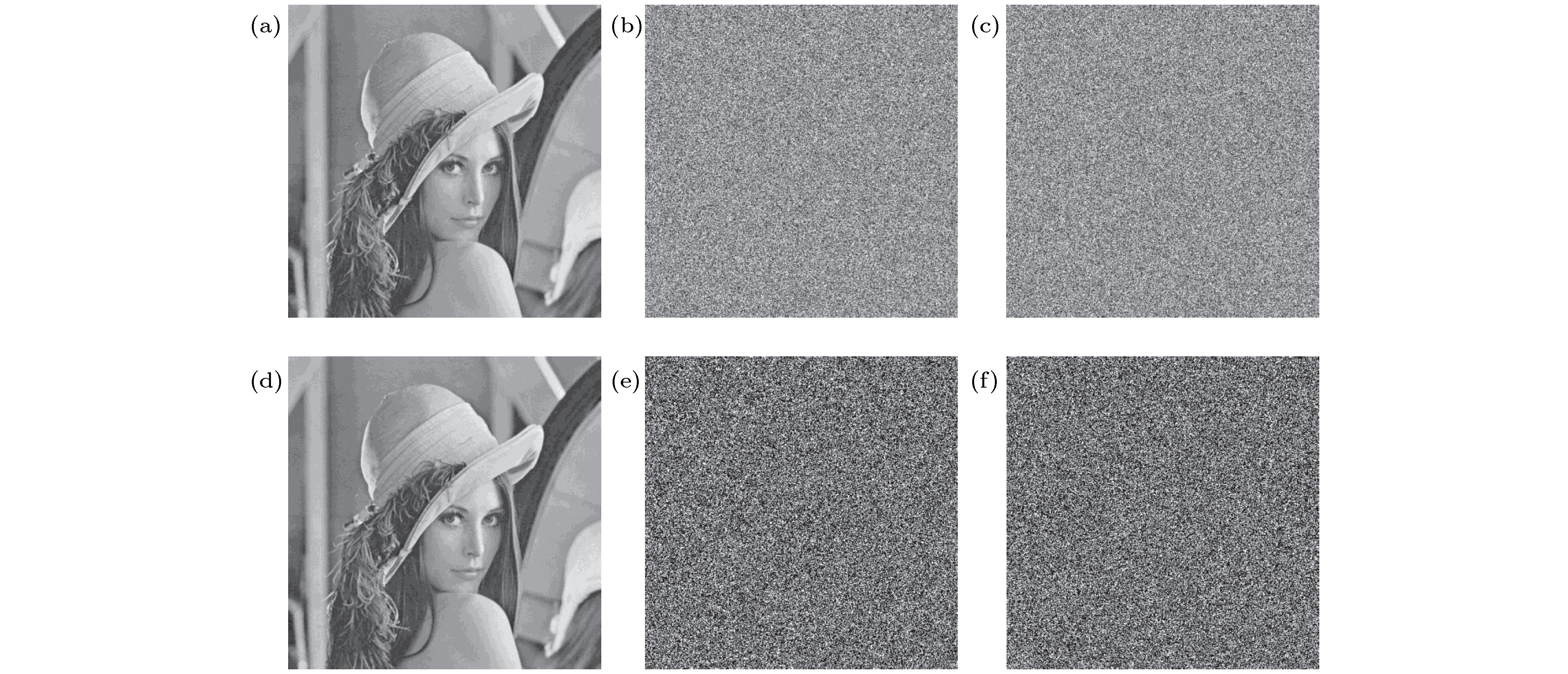
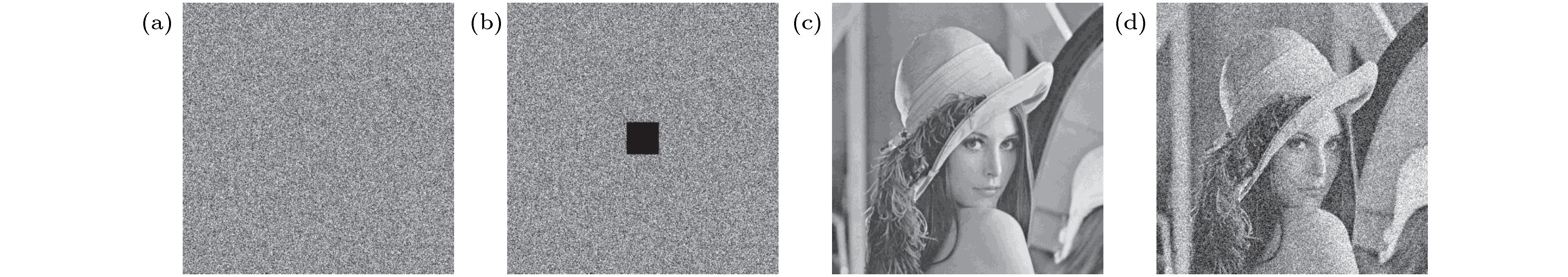
$x \text- y$ flat; (b)$x \text- z$ flat; (c)$x \text- v$ flat; (d)$y \text- z$ flat; (e)$y \text- w$ flat; (f)$z \text- w$ flat; (g)$z \text- v$ flat.图 6 数字图像加解密实验图 (a) lena原图; (b) lena加密图像; (c) lena解密图像; (d) baboon原图; (e) baboon加密图像; (f) baboon解密图像; (g) boat原图; (h) boat加密图像; (i) boat解密图像
Fig. 6. Digital image encryption and decryption experiment: (a) Original Lena image; (b) encrypted Lena image; (c) decrypted Lena image; (d) original baboon image; (e) encrypted baboon image; (f) decrypted baboon image; (g) original boat image.; (h) encrypted boat image; (i)decrypted boat image.
图 7 明文图像和密文图像直方图 (a) lena明文直方图; (b) lena密文直方图; (c) baboon明文直方图; (d) baboon密文直方图; (e) boat明文直方图; (f) boat密文直方图
Fig. 7. Histogram of plaintext and ciphertext images (a) Plaintext Lena image histogram; (b) ciphertext Lena image histogram; (c) plaintext baboon image histogram; (d) ciphertext baboon image histogram; (e) plaintext boat image histogram; (f) ciphertext boat image histogram.
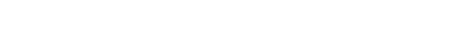
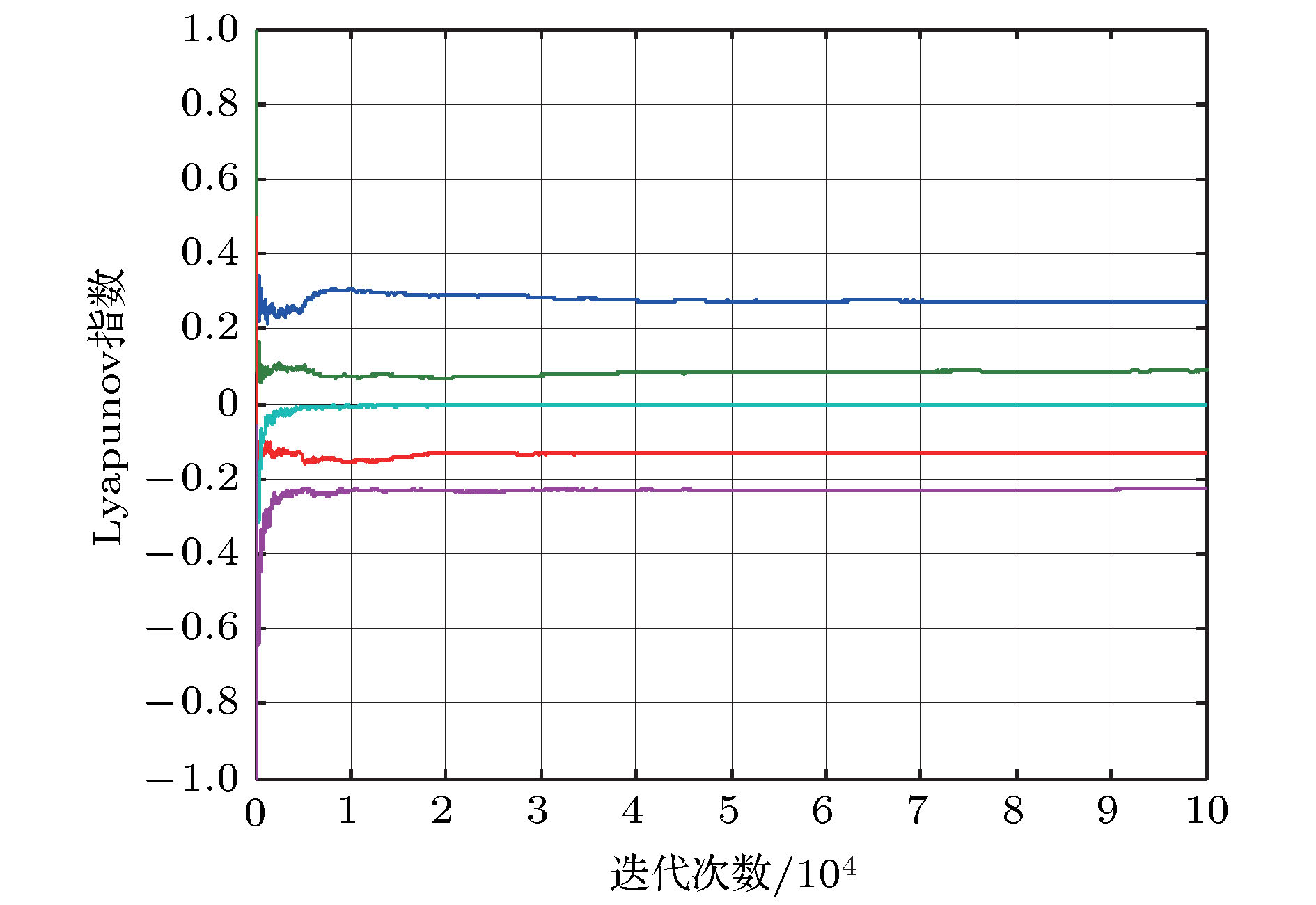
图 8 密钥敏感性测试图 (a)明文图像; (b)密文
${{{Y}}_1}$ (密钥为${y_0}$ ); (c)密文${{{Y}}_2}$ (密钥为${y_1}$ ); (d)${{{Y}}_1}$ 正确解密结果; (e)${{{Y}}_1}$ 用${y_1}$ 错误解密结果; (f)${{{Y}}_2}$ 用${y_0}$ 错误解密结果Fig. 8. Key sensitivity tests: (a) Plain-image; (b) cipher
${{{Y}}_1}$ with key${y_0}$ ; (c) cipher${{{Y}}_2}$ with key${y_1}$ ; (d) right decrypted${{{Y}}_1}$ ; (e) decrypted${{{Y}}_1}$ with${y_1}$ ; (f) decrypted${{{Y}}_2}$ with${y_0}$ .表 1 明文图像与加密图像的信息熵分析表
Table 1. Information entropy analysis table of plain text and encrypted image.
表 2 加密图像不动点比分析表
Table 2. Encrypted image fixed point ratio analysis table.
图像 总像素数 不动点数 不动点比 Lena图像 262144 1015 0.39% Baboon图像 262144 1014 0.39% Boat图像 262144 999 0.38% 表 3 灰度平均变化值分析表
Table 3. Grayscale average change value analysis table.
图像 Lena图像 Baboon图像 Boat图像 灰度平均变化值 73.1937 70.8589 74.8383 表 4 密钥敏感性测试结果表
Table 4. Key sensitivity test result table.
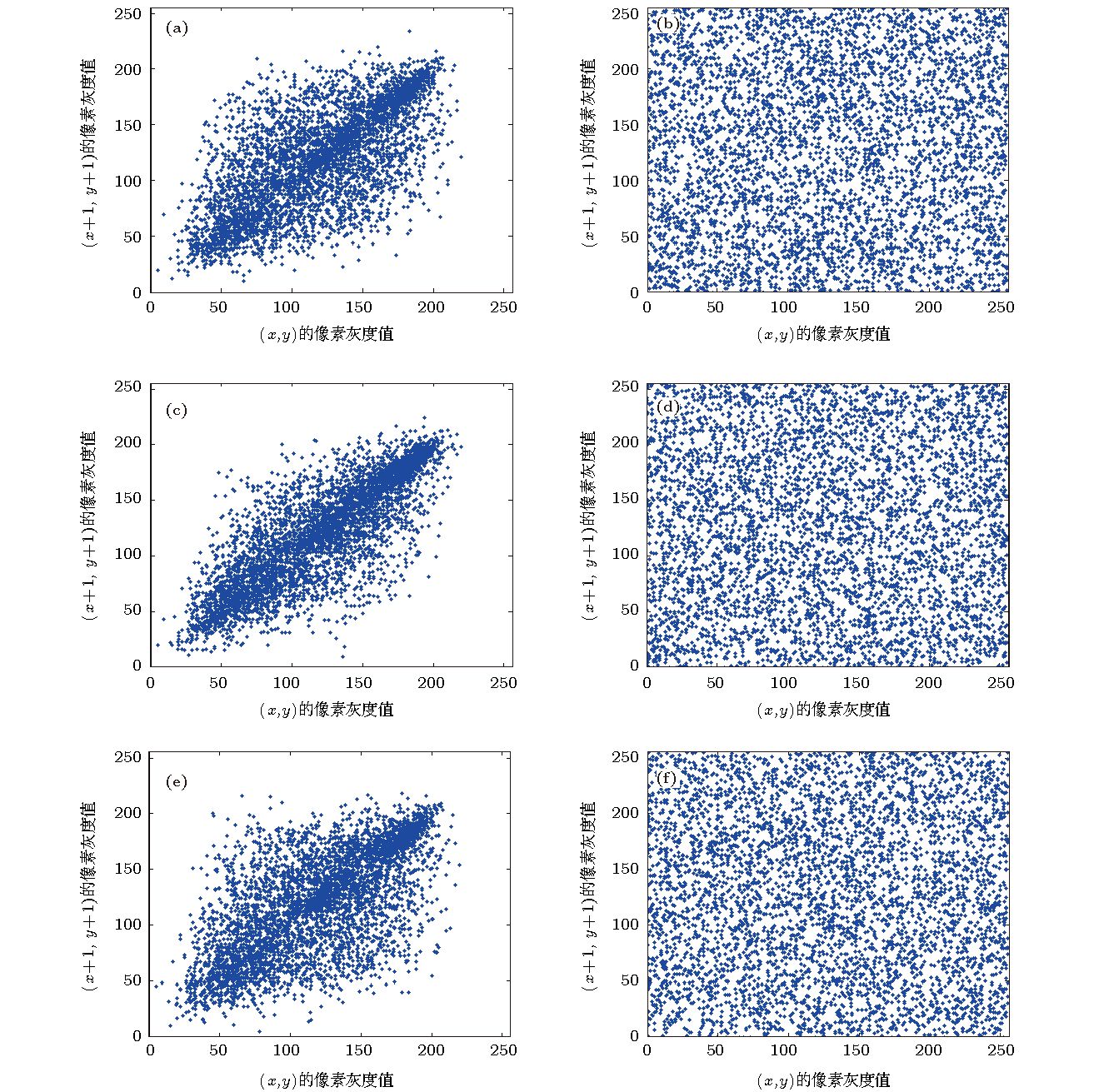
表 5 明文图像与密文图像相关系数测试结果表
Table 5. Plaintext image and ciphertext image correlation coefficient test result table.
图像 水平方向相关系数 垂直方向相关系数 对角线方向相关系数 明文图像 密文图像 明文图像 密文图像 明文图像 密文图像 Lena 0.9762 –0.0084 0.9659 0.0461 0.9468 0.0131 Baboon 0.7204 –0.0050 0.8264 –0.0074 0.7046 –0.0322 boat 0.9621 0.0106 0.8252 0.0087 0.8327 –0.0423 -
[1] 王平, 冯勇, 孙黎霞, 韩凤玲 2002 控制理论与应用 21 1
 Google Scholar
Google Scholar
Wang P, Feng Y, Sun L X, Han F L 2002 Control Theory & Appl. 21 1
 Google Scholar
Google Scholar
[2] 禹思敏 2005 54 1500
 Google Scholar
Google Scholar
Yu S M 2005 Acta Phys.Sin. 54 1500
 Google Scholar
Google Scholar
[3] Karthikeyan R, Serdar C, Peiman N, Abdul J M, Sajad J, Anitha K 2018 Eur. Phys. J. Plus 133 354
 Google Scholar
Google Scholar
[4] 贾美美, 蒋浩刚, 李文静 2019 68 130503
 Google Scholar
Google Scholar
Jia M M, Jiang H G, Li W J 2019 Acta Phys. Sin. 68 130503
 Google Scholar
Google Scholar
[5] Li Y X, Tang W K S, Chen G R 2005 Int. J. Bifurcation Chaos. 15 3367
 Google Scholar
Google Scholar
[6] 彭再平, 王春华, 林愿, 骆小文 2014 63 240506
 Google Scholar
Google Scholar
Peng Z P, Wang C H, Lin Y, Luo X W 2014 Acta Phys. Sin. 63 240506
 Google Scholar
Google Scholar
[7] 刘杨 2015 博士学位论文 (哈尔滨: 哈尔滨工业大学)
Liu Y 2015 Ph. D. Dissertation (Harbin: Harbin Institute of Technology) (in Chinese)
[8] 禹思敏 2018 新型混沌电路与系统的设计原理及其应用 (北京: 科学出版社) 第139—155页
Yu S M 2018 Design Principles and Applications of New Chaotic Circuits and Systems (Beijing: Science Press) pp139– 155 (in Chinese)
[9] Zhang L H, Liao X F, Wang X B 2005 Chaos, Solitons Fractals 24 759
 Google Scholar
Google Scholar
[10] Wong K, Kwor B, Law W 2008 Phys. Lett. A 372 2645
 Google Scholar
Google Scholar
[11] Zhang W, Yu H, Zhao Y L, Zhu Z L 2016 Signal Process. 118 36
 Google Scholar
Google Scholar
[12] Luo Y L, Zhou R L, Liu J X, Gao Y, Ding X M 2018 Nonlinear Dyn. 4 1
[13] Ye G D, Pan C, Huang X L, Mei Q X 2018 Nonlinear Dyn. 20 18
[14] Abanda Y, Tiedeu A 2016 IET Image Proc. 10 742
 Google Scholar
Google Scholar
[15] Zhang Y 2018 Inf. Sci. 255 31145
[16] He Y, Zhang Y Q, Wang X Y 2018 Neural Comput. Appl. 10 1
[17] Raza S F, Satpute V 2018 Nonlinear Dyn. 254 1
[18] Ahmad J, Khan M A, Hwang S O, Khan J S 2017 Neural Comput. Appl. 28 953
[19] Ahmad J, Khan M A, Ahmed F, Khan J S 2018 Neural Comput. Appl. 3 1
[20] Sprott J C 1994 Phys. Rev. E 50 647
 Google Scholar
Google Scholar
[21] Enayatifar R, Abdullah A H, Isnin I F, Altameem A, Lee A 2017 Opt. Lasers Eng. 90 146
 Google Scholar
Google Scholar
[22] Liu H J, Wang X Y, Kadir A 2012 Appl. Soft Comput. 12 1457
 Google Scholar
Google Scholar
计量
- 文章访问数: 12534
- PDF下载量: 250
- 被引次数: 0












 下载:
下载: